Emerging Threats Create Exposure Gaps
When threats like React2Shell emerge, assessing exposure across every environment takes days of analyst time — a window that attackers exploit long before teams can close it.
AI Threat Hunter runs federated, hypothesis-driven threat hunts across your SIEM, EDR, and cloud 24/7. No analyst time required.
The next agent joining the Dropzone AI team, launching Summer 2026.
Trusted by 300+ security teams including

.webp)


Security teams have always wanted to hunt proactively. But thorough threat hunting demands time, expertise, and cross-tool investigation that most teams can't sustain alongside their daily workload. Until now, continuous hunting was a luxury only the largest, best-resourced SOCs could afford.
When threats like React2Shell emerge, assessing exposure across every environment takes days of analyst time — a window that attackers exploit long before teams can close it.
A thorough hunt takes 10+ hours of cross-tool investigation. Most teams run a handful per quarter. Not for lack of skill, but because continuous hunting demands more analyst hours than any team can spare.
Tell AI Threat Hunter what to hunt, or choose from a catalog of curated hunt packs built by Dropzone's threat research team. Either way, the agent does the work: generating hypotheses, testing them across your full security stack, and following the evidence. 24/7, without analyst time during execution.
Manual Threat Hunting:
10-20 hours per hunt
AI Threat Hunter:
~60 minutes per hunt cycle
Analyst time required:
Zero during execution
Federated search across all your tools casts a wide net for every data source the hunt requires — SIEM, EDR, cloud, identity — simultaneously. A single search can return up to half a million rows of telemetry.
AI Threat Hunter slices that data in thousands of ways in parallel using data science and LLMs, boiling results down to the anomalies that matter. This is computing doing what computing does best — processing data at a scale no human analysis workflow can match.
Each lead typically takes 10-20 minutes of manual analyst time. AI Threat Hunter pursues dozens of deep-dive investigations in parallel to confirm whether anomalies represent real threats. Hunt reports also surface non-attack insights — misconfigurations, shadow IT, and vulnerabilities — even when no active attacker is found.

Hunting for indicators of compromise from just-released intelligence before they become widespread attacks.

Intelligence-driven hunts that map your logs against the known behaviors of groups like Scattered Spider and Lazarus.

Going beyond scanning to hunt for evidence of active exploitation of critical CVEs within your environment.

Lateral movement, persistence, living-off-the-land — the techniques that live below the detection threshold.
Detecting abuse of legitimate business logic, from MFA fatigue attacks to unusual administrative overrides.
AI Threat Hunter queries your SIEM, EDR, cloud, and identity tools via API — the same way your analysts do. No vendor lock-in. Federated hunts across 90+ integrations mean every hunt draws from your full security context, not just one vendor's ecosystem.
Intelligence triggers hunting. Hunting triggers investigation. Works autonomously without requiring human prompting. AI Threat Hunter operates in a closed loop with AI Threat Intel Analyst and AI SOC Analyst. Agents collaborating at machine speed, 24/7.

300+ deployments. 160 years of manual alert analysis automated. Enterprises, MSSPs, and organizations working in the federal space.
AI Threat Hunter launches Summer 2026. Early access is available to select security teams. Request access to get:
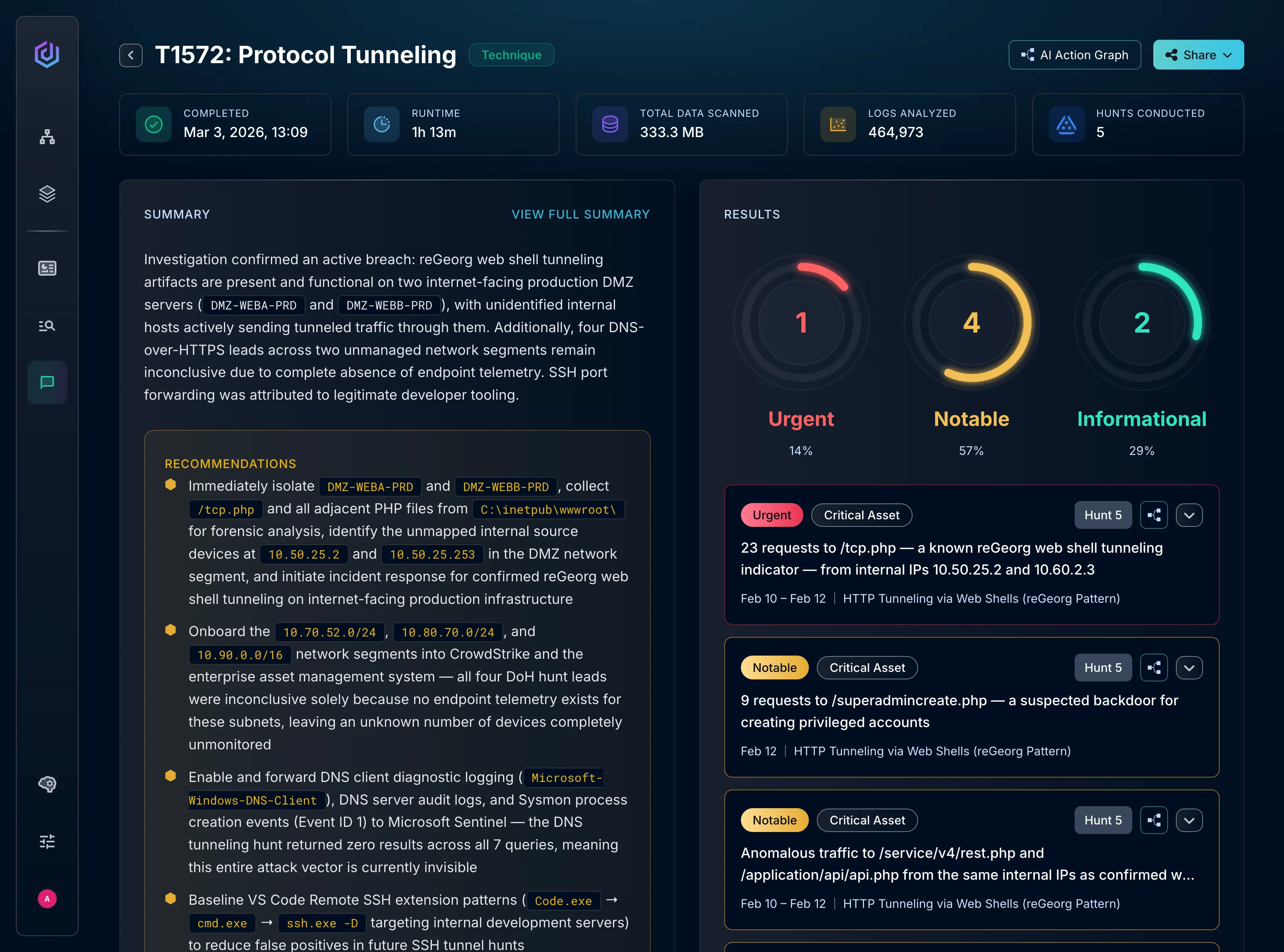
AI Threat Hunter is an autonomous AI agent that runs federated, hypothesis-driven threat hunts across your SIEM, EDR, and cloud environments. It selects from a curated library of hunt packs, tests hypotheses against your data, and delivers findings without requiring analyst time during execution. It's the next agent joining Dropzone's Agentic SOC.
AI Threat Hunter runs a three-phase pipeline at machine scale. Search at Scale casts a wide net via federated lookups across 90+ integrations — a single hunt can surface up to half a million rows of telemetry. Filter at Scale processes that data in parallel using data science and LLMs to surface only meaningful anomalies. Investigate at Scale pursues dozens of deep-dive investigations simultaneously — work that would take a human analyst 10-20 minutes per lead, completed in parallel across every finding.
Five categories: Emerging Threats (indicators of compromise from just-released intelligence), Threat Actors (behaviors of groups like Scattered Spider and Lazarus mapped against your logs), Vulnerabilities (active exploitation of critical CVEs, not just scanning), ATT&CK Techniques (lateral movement, persistence, living-off-the-land below the detection threshold), and Operational Anomalies (abuse of legitimate business logic, from MFA fatigue to unusual administrative overrides).
Manual threat hunts require experienced analysts to switch between tools, build queries, and manually correlate results. That process typically takes 10+ hours per hunt. AI Threat Hunter completes the same process autonomously in under two hours, and runs continuously rather than episodically. Your team directs the strategy. The agent handles the execution.
No. AI Threat Hunter handles the manual, repetitive investigation work: cross-tool querying, log correlation, and evidence gathering that consumes most of a hunt. Your analysts focus on hypothesis development, detection engineering, and strategic response. Dropzone elevates people. It doesn't replace them.
AI Threat Hunter connects to 90+ integrations across SIEM, EDR, XDR, cloud environments, and identity platforms. It queries your tools via API, the same way your human analysts do. No data lift, no log normalization required. Your data stays where it is.
AI Threat Hunter launches Summer 2026. Request early access above to get priority access to demos, early builds, and dedicated onboarding.
AI Threat Hunter is built on the Dropzone AI platform. Contact us to discuss deployment options for new and existing customers.