Connect Your Security Stack. AI SOC Agents Do the Rest.
Dropzone AI connects to your SIEM, EDR, cloud, identity, email, and other security tools. AI SOC agents use your existing tools expertly to investigate every alert, no data migration required.
90+
integrations
300+
deployments worldwide
Ready in hours
not weeks

Gartner Cool Vendor for the Modern SOC
Works With the Tools Your Team Already Uses













.svg)


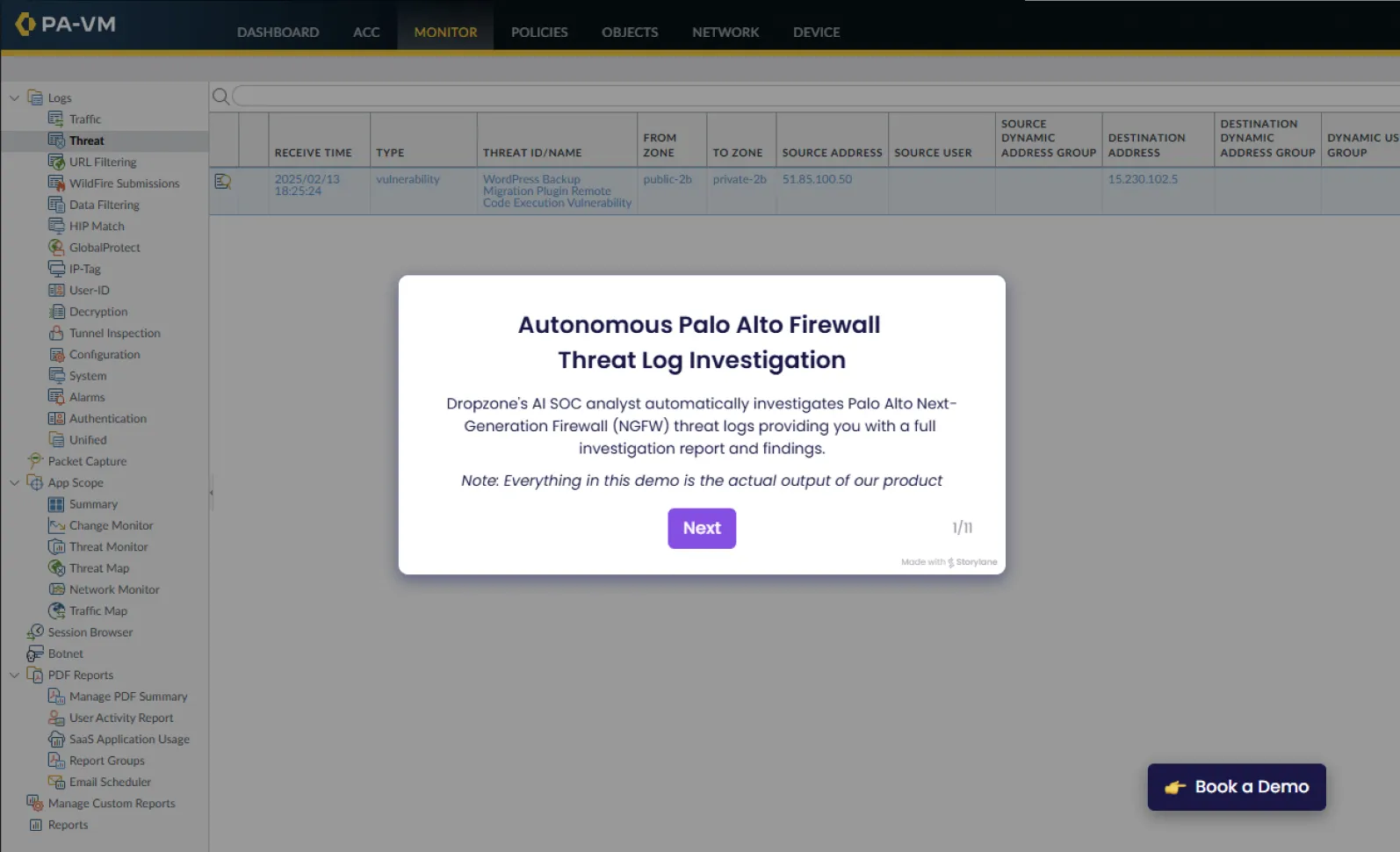
See How AI Agents Investigate Alerts Across Your Stack
Don't See Your Tool?
We add new integrations regularly based on customer demand. Tell us what you need.
Frequently Asked Questions
Dropzone AI integrates with 90+ security tools across 14 categories: SIEM (Splunk, Microsoft Sentinel, Google Security Operations, QRadar), endpoint (CrowdStrike, Microsoft Defender, SentinelOne), cloud (AWS, Azure, Google Cloud, Wiz), identity (Okta, Entra ID), email, network, SOAR, threat intelligence, and more. New integrations ship regularly.
Dropzone AI connects through native API integrations. AI agents query your tools directly, the same way a human analyst would pull data from Splunk or CrowdStrike during an investigation. There is no data migration, no log normalization, and no custom connectors to build. You grant API access, and agents start investigating alerts using your existing data.
No. Most integrations are configured through API key or OAuth authentication in the Dropzone console. No scripts, no custom code, no professional services engagement. Teams typically connect their core tools and begin investigating alerts within hours of deployment.
Yes. The Dropzone Alert Ingest API accepts alerts from any source that can send a webhook or API call. If your custom application generates security alerts, Dropzone AI agents can investigate them. For tools not yet on the integration list, submit a request and the team will evaluate it.
Most integrations take minutes to configure. The typical deployment connects 3-5 core tools (SIEM, EDR, identity, cloud) and begins investigating alerts within hours, not weeks. There is no data migration, no playbook authoring, and no tuning period. AI agents learn your environment through natural-language coaching after deployment.
Alert volume is growing faster than security teams can hire. Dropzone AI agents investigate every alert across your full tool stack, 24/7, at machine speed. Teams that deploy Dropzone see 5x faster MTTR and 85% reduction in manual alert investigation, which frees analysts to focus on threat hunting, detection engineering, and strategic security work instead of alert triage.
Ready to See Dropzone AI Work With Your Stack?
We add new integrations regularly based on customer demand. Tell us what you need.