IOCs Are Easy. TTPs Are Not.
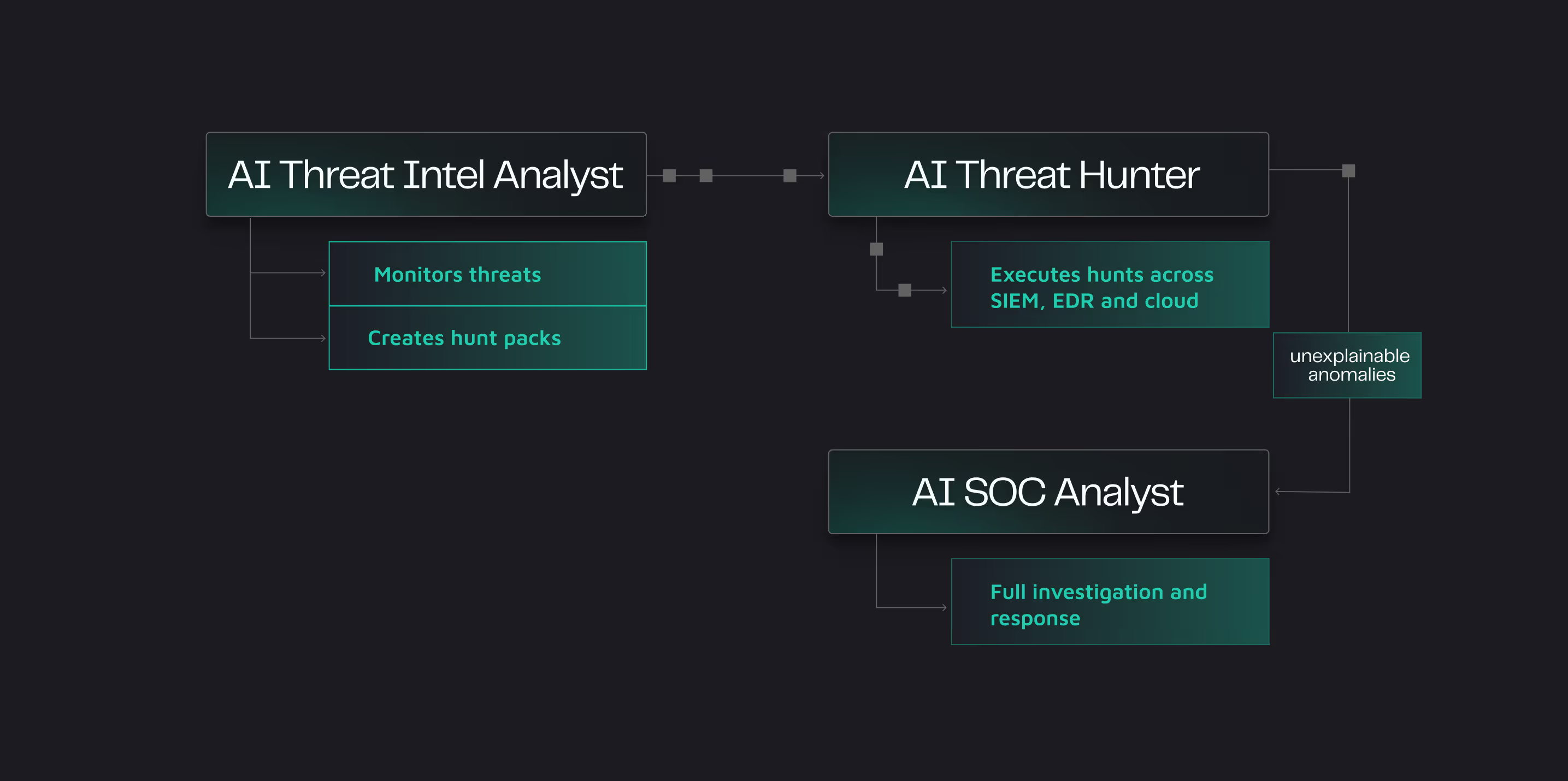
Extracting IP addresses and file hashes from a CISA advisory is straightforward. Mapping behavioral techniques to MITRE ATT&CK and turning them into hunt logic that your SOC can act on? That takes hours of skilled analyst work.

.webp)