Need a relentless network alert analyst?
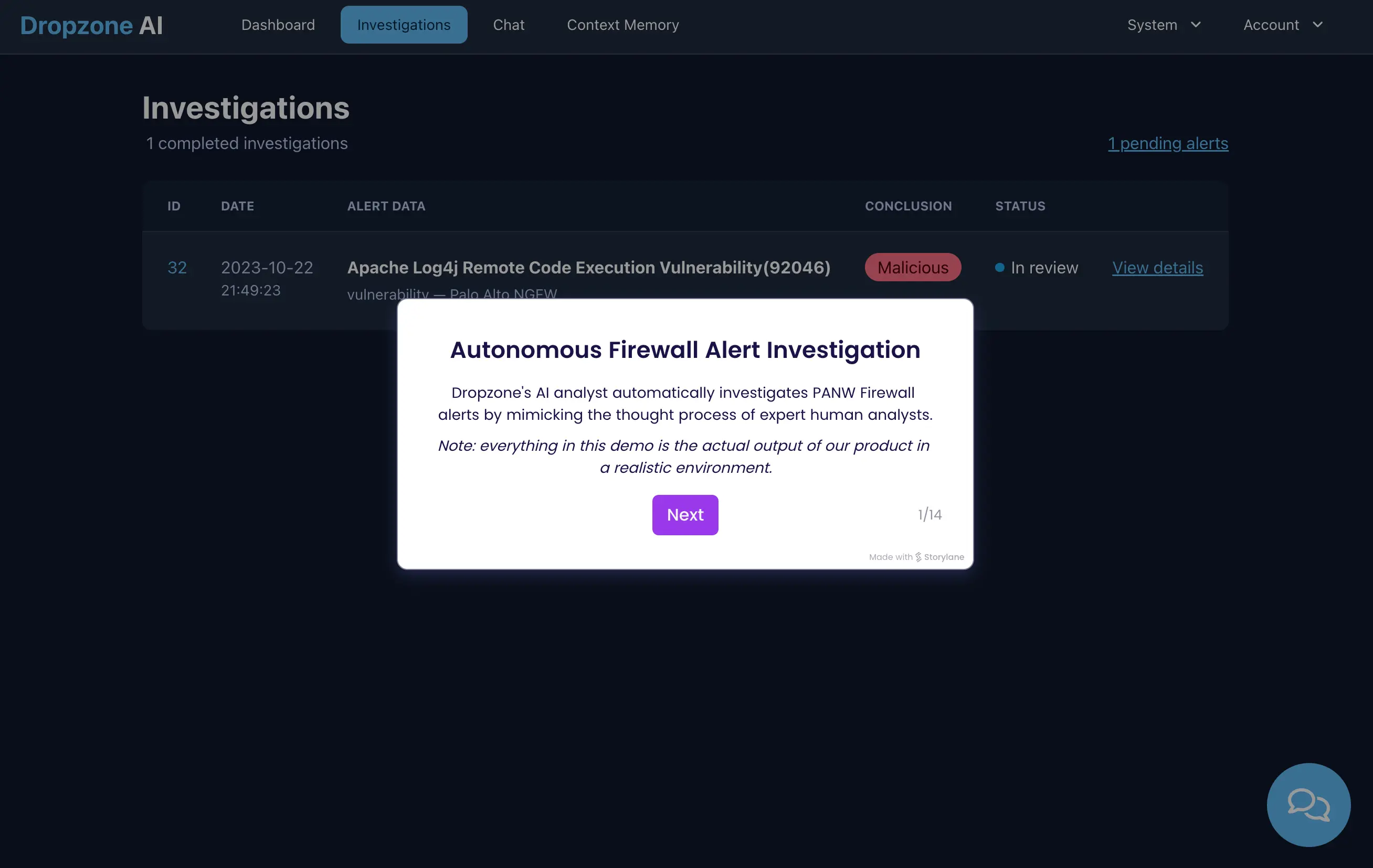
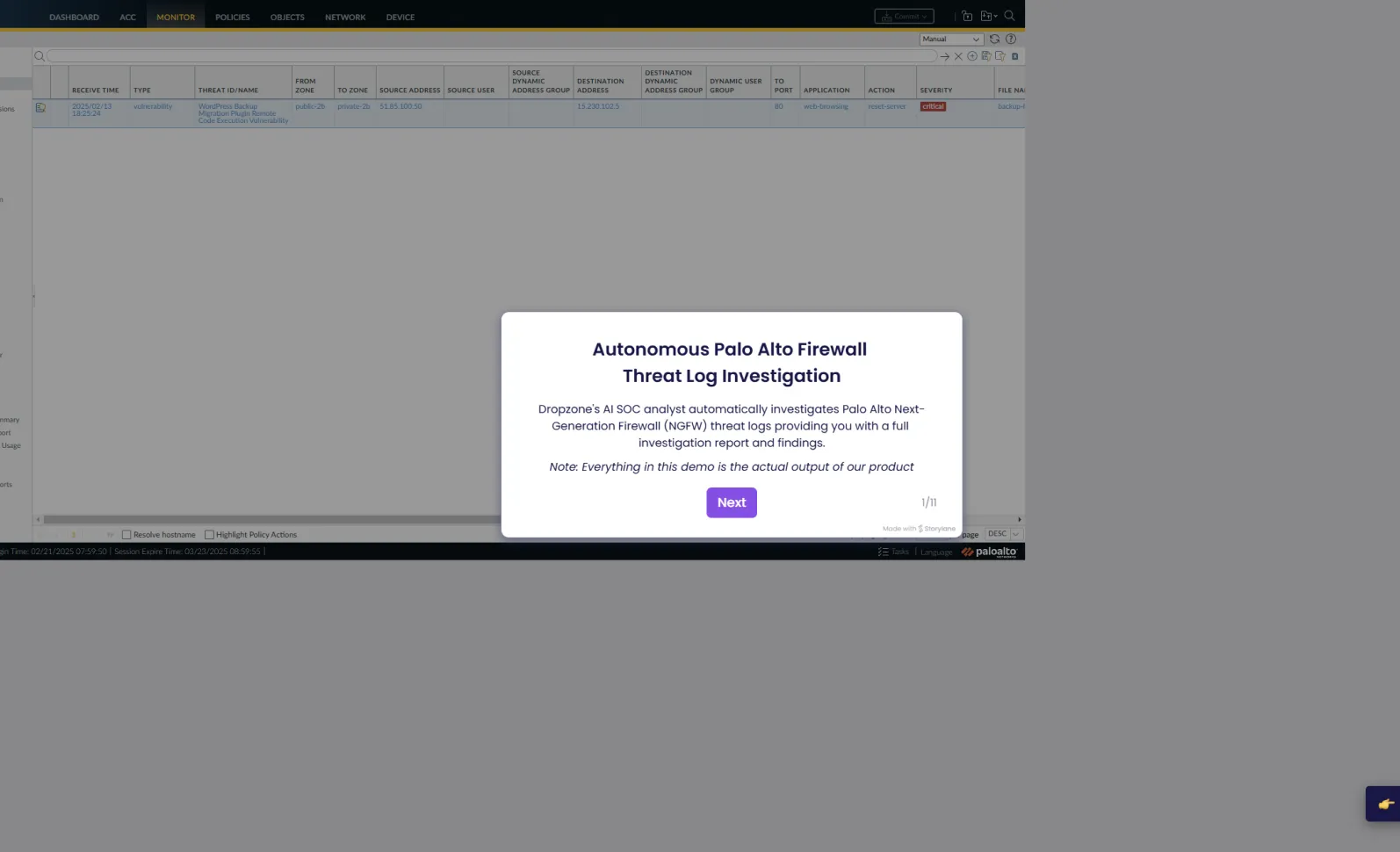
Dropzone’s specialized AI agent performs end-to-end investigations and generates fast, detailed and accurate reports for every network alert.
5x
faster mean time to respond
85%
reduction in manual alert investigation
300+
deployments worldwide

Gartner Cool Vendor for the Modern SOC
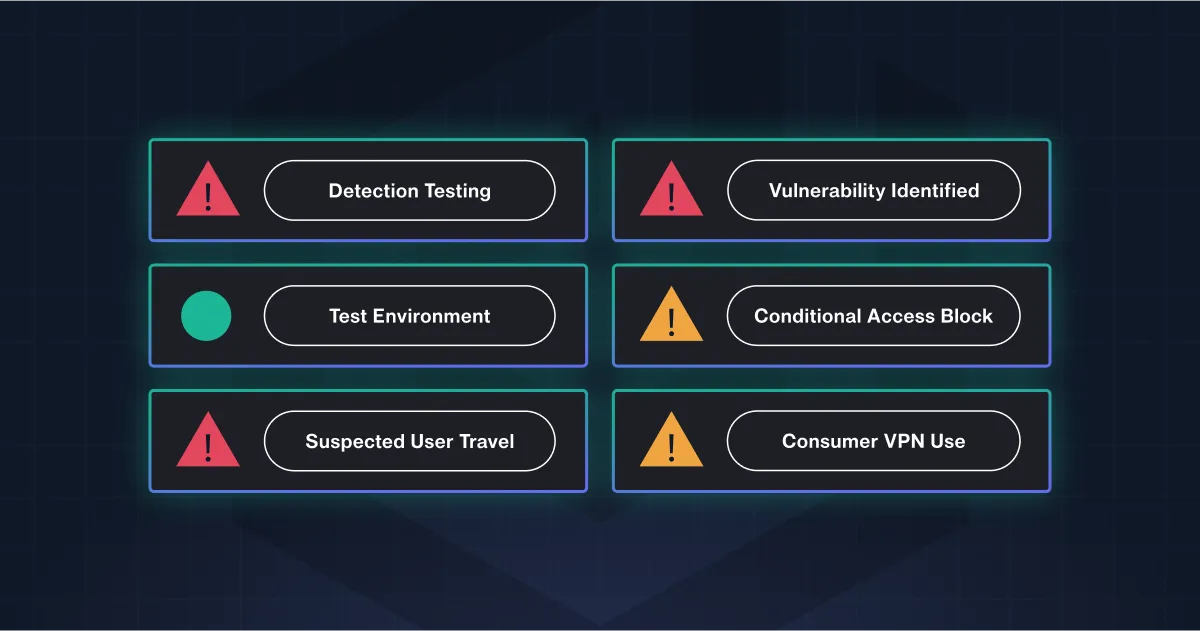
Dropzone investigates all network alerts, mimicking the thought process of expert analysts.
Collect
For each investigation, Dropzone pulls relevant data from your IDS, FW, SIEMs and other security data sources, such as network logs.
Comprehend
Dropzone leverages LLMs, its security pre-training, your various logs and organizational context. It then draws correlations and reaches definitive conclusions.
Conclude
Dropzone generates full reports with severity conclusion, executive summaries and key evidence.
Integrations
Dropzone integrates with your security tools and data stack to comprehend your full security context.
















Reduce manual alert analysis time by 95%
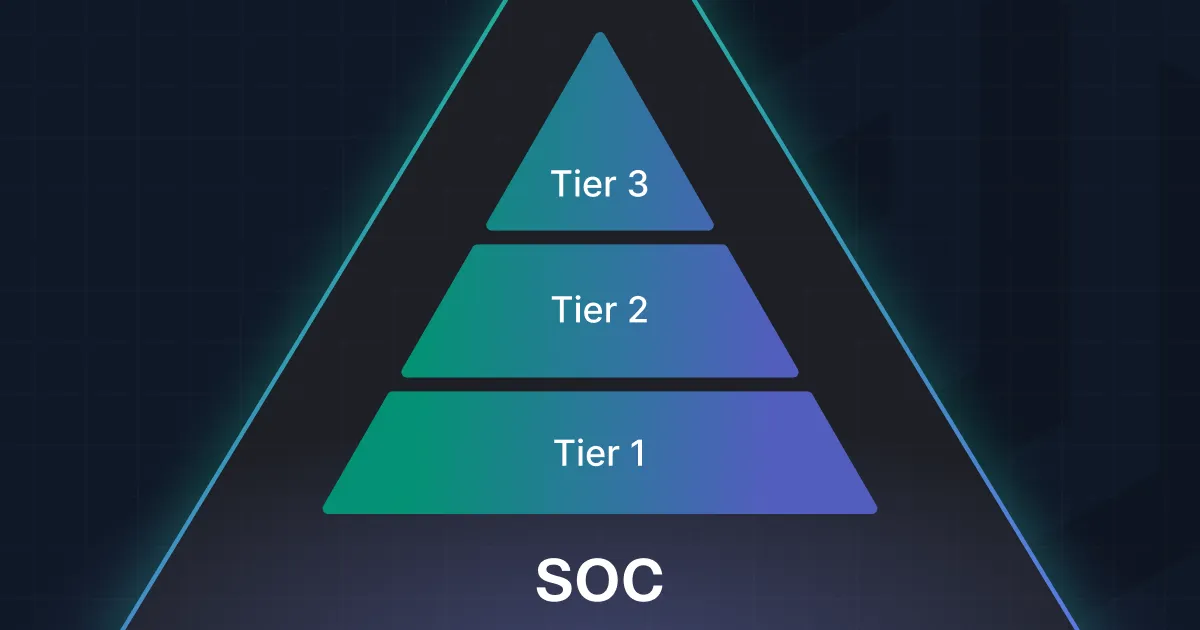
When Dropzone handles investigations, your analysts can focus on addressing the real threats.
Reduce MTTR
Fast forward your triage, investigation, and response down to minutes.
Focus on real threats
Get to more consistent and accurate conclusions with Dropzone’s detailed investigations.
Free your analysts for higher-value work
Make each investigation and response more contextual to your customer’s specific environment.
Want to test drive
Dropzone AI?
Note about privacy:
- All emails are deleted after analysis
- No emails will be used to train AI models
- We will collect the email address that is submitted and add it to our mailing list. You may unsubscribe at any time.
By using our service, you agree to the above
Forward a suspicious email to scan@try-dropzone.ai

Dropzone AI Investigates

Receive Tailored Report

- All emails are deleted after analysis
- No emails will be used to train AI models
- We will collect the email address that is submitted and add it to our mailing list. You may unsubscribe at any time.
By using our service, you agree to the above
Get a sample report



.webp)


.webp)


.webp)