MTTR Under 10 Minutes—Every Alert, Every Time
Dropzone AI’s autonomous SOC agents deliver context-rich investigations in minutes—so threats are contained before they escalate.
5x
faster MTTR
90
integrations
300+
deployments worldwide

Gartner Cool Vendor for the Modern SOC
What Happens When Alerts Sit in a Queue?
Every minute an alert sits unexamined, the attacker's lead grows. In 2017, Merck suffered $1.4 billion in damages from the NotPetya attack, compounded by delayed response. Modern threat actors are faster: Scattered Spider has demonstrated the ability to compromise an environment in under 30 minutes from initial access.
The math is simple. If your SOC takes half an hour to investigate a single alert, and you receive hundreds per day, the backlog becomes a business risk. Attackers are not waiting for your queue to clear.
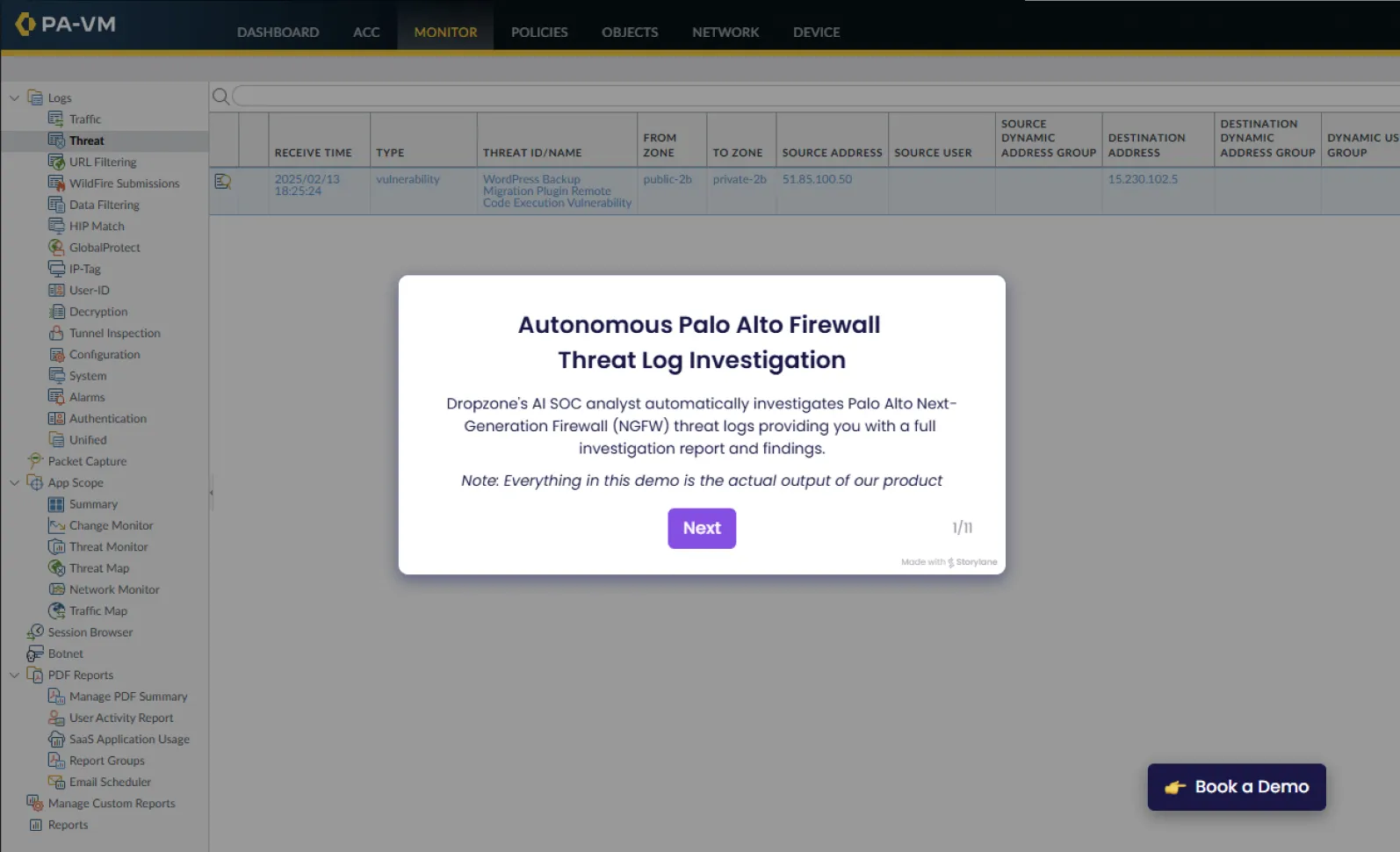
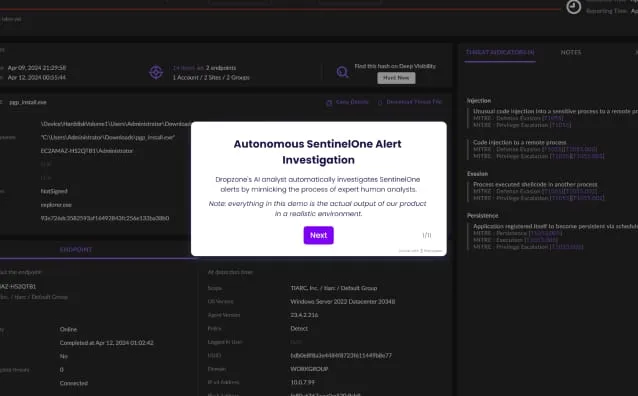
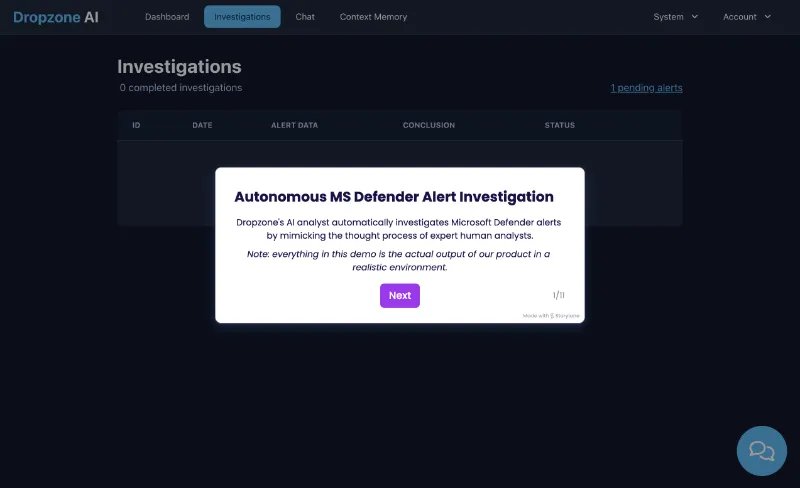
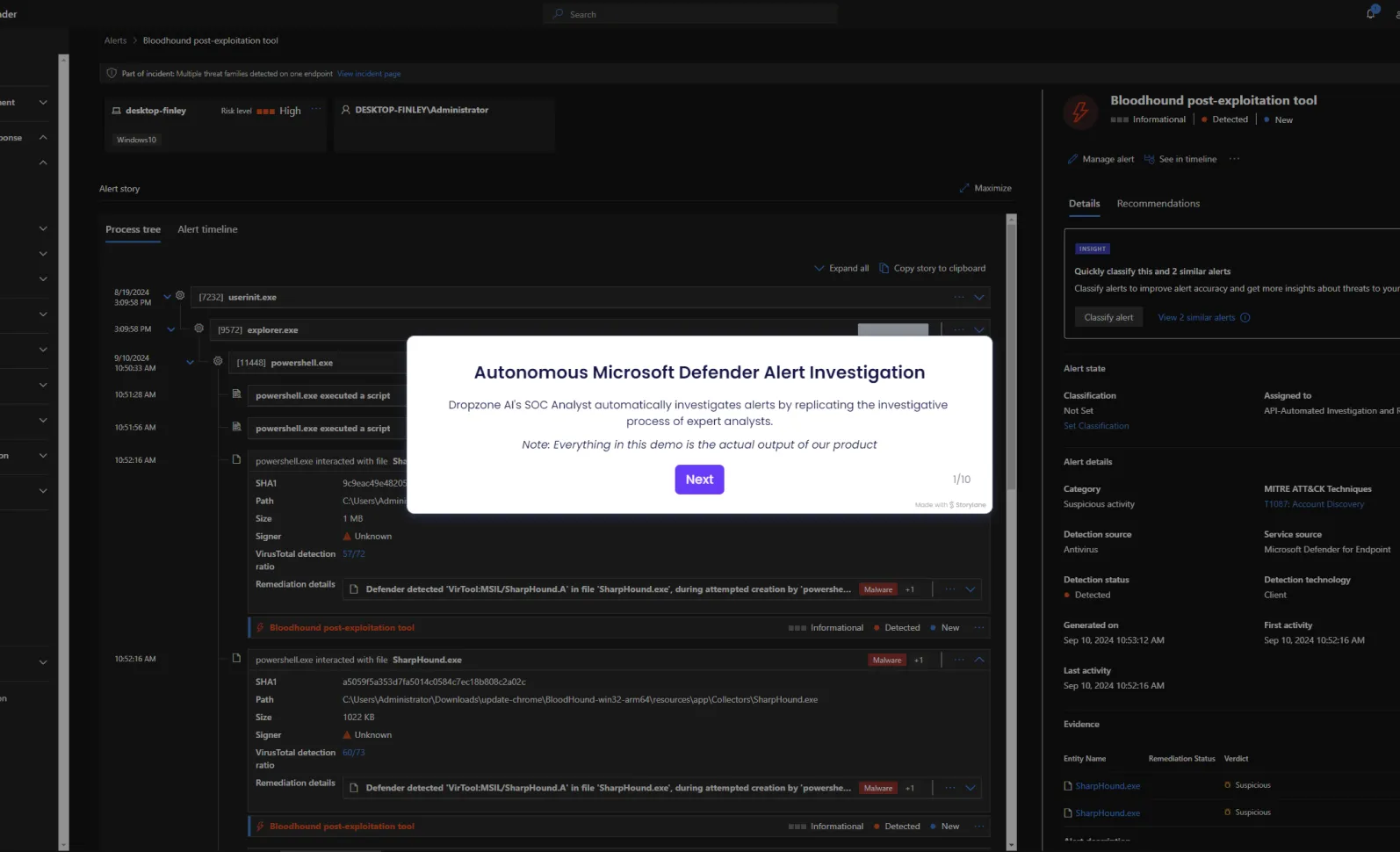
How It Works
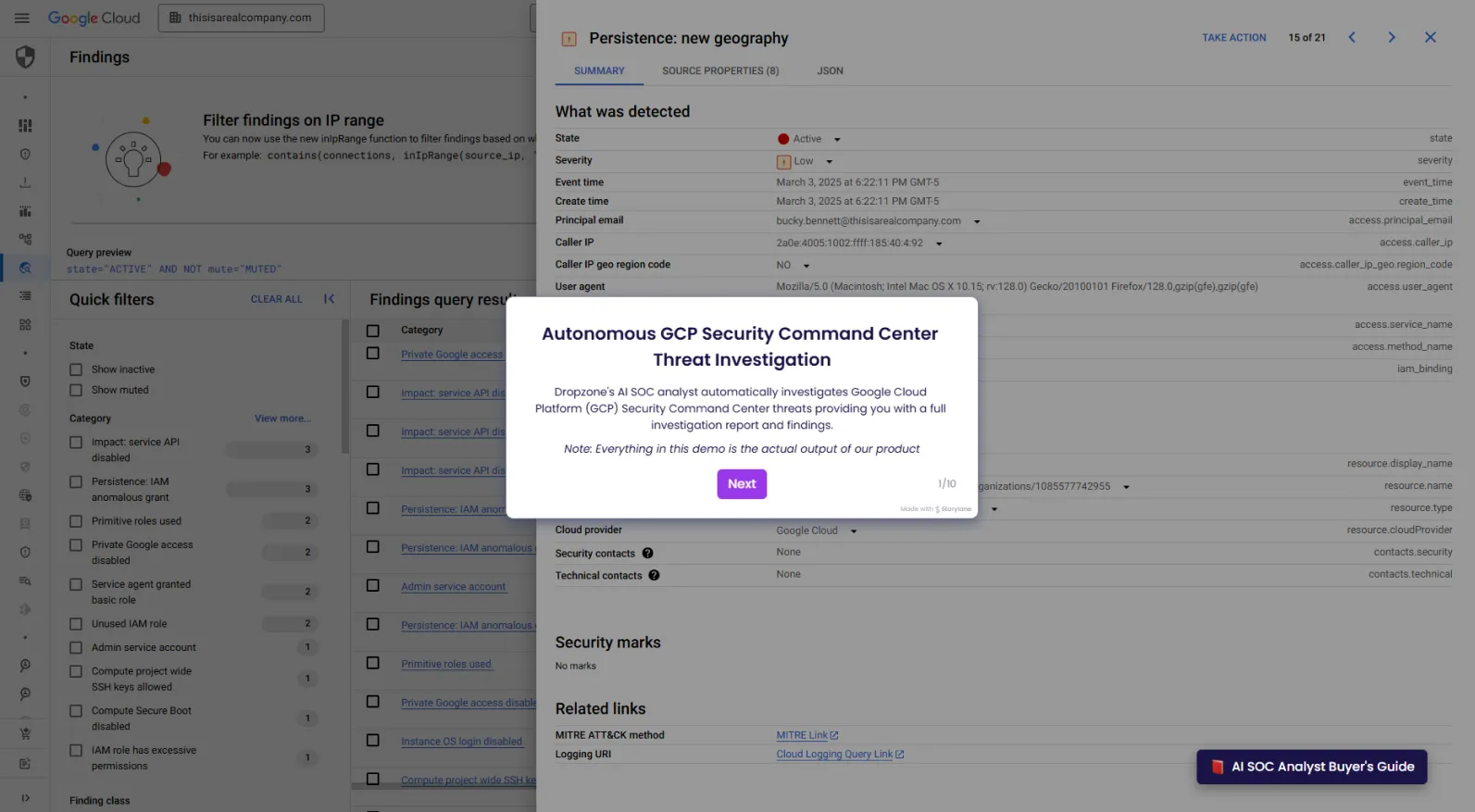
Why Is Reasoning-Based Investigation Faster Than SOAR?
Traditional SOAR platforms rely on static playbooks: predefined rules that execute when conditions match. When alerts fall outside those rules, the playbook breaks and the alert goes back to a human queue. That queue is where MTTR dies.
Dropzone AI takes a different approach. AI agents reason through each investigation dynamically, querying tools, correlating evidence, and following investigative threads the way a seasoned analyst would. No predefined rules to maintain. No automation engineers to write playbooks. Every alert gets investigated, regardless of whether it matches a template.
Dropzone AI Doesn’t Just Automate—
It Reasons
- Triages and investigates alerts using reasoning, not static rules
- Understands context—phishing content, unusual behavior, attacker techniques
- Interviews users when necessary to gather first-hand input
- Shows its work with detailed findings and evidence
What Does Sub-10-Minute MTTR Mean for Your Organization?
Faster Response, Lower Risk
Every minute shaved off MTTR reduces the attacker's window to move laterally, exfiltrate data, or deploy ransomware. Organizations using Dropzone AI report 5x faster mean time to respond and 90% faster escalated investigations.
100% Alert Coverage, Zero Backlog
AI agents investigate every alert that fires, 24/7. No triage queue. No alert fatigue. No coverage gaps during shift changes, holidays, or staff turnover.
Contain Threats Before They Spread
When AI agents confirm a threat, containment actions fire immediately: blocking IPs, disabling compromised accounts, isolating endpoints. Threats are contained in minutes, not hours.
Works With Your Existing Security Stack
Dropzone AI integrates with 90+ security tools via native APIs. No data migration. No log normalization. No playbooks to build. AI agents query your SIEM, EDR, identity, cloud, and business systems directly to gather context, the same way your human analysts do. Complements existing SOAR implementations rather than replacing them.
How Much Does Slow Response Time Cost Your Organization?
Use the calculators below to estimate the financial impact of faster alert investigation and response. Benchmarks are based on IBM's 2024 Cost of a Data Breach Report.
Data Breach Risk Reduction

Increased Alert Coverage

Per-Hour Damage Mitigation

Frequently Asked Questions
Dropzone AI investigates every alert in minutes, regardless of alert type or source tool. AI agents begin investigation immediately when an alert fires, querying your SIEM, EDR, identity, and cloud tools to gather evidence. Organizations report 5x faster mean time to respond compared to manual investigation workflows.
MTTR stands for mean time to respond (or mean time to remediate). It measures the average time from alert detection to containment or resolution. Lower MTTR directly reduces the window attackers have to move laterally, exfiltrate data, or deploy ransomware. Industry benchmarks show that faster containment correlates with lower breach costs.
SOAR platforms depend on static playbooks written by automation engineers. When an alert falls outside a predefined rule, it goes back to a human queue. AI agents reason dynamically through each investigation, adapting to new alert types without requiring new playbooks. This eliminates the maintenance burden and covers alert types that static rules cannot handle.
Yes. When AI agents confirm a threat, containment actions fire immediately. This includes blocking malicious IPs, disabling compromised user accounts, and isolating affected endpoints. Containment is based on the investigation evidence, not a static rule, so the action matches the threat.
Dropzone integrates with 90+ security tools through native APIs. AI agents query your tools directly during investigations, the same way a human analyst would. No data migration, no log normalization, and no custom connectors to build. Most teams deploy within hours.
The ROI calculators on this page use IBM's 2024 Cost of a Data Breach Report and Dropzone customer results as benchmarks. They estimate risk reduction, alert coverage value, and per-hour damage mitigation based on your organization's alert volume, current investigation capacity, and estimated cost per hour of an active breach.