Say that you’re a police detective who never investigates suspects without a criminal record. Whenever a person becomes a suspect, you look at their clean history and decide to give them a pass. The verdict: You’re a lousy detective.
Yet this type of shallow investigation is common practice in cyber defense. Most SOC teams use threat intelligence (TI) to enrich their alerts. This works great when there is a match with a known-bad indicator of compromise (IOC): an IP address, domain, or file hash. These are strong signals of a true positive.
But what about when there isn’t a match? While TI sources are extremely useful in identifying true positives, they are very doubtful indicators of true or false negatives. In the field of machine learning and statistical calculation, we call this type of categorization the confusion matrix. The problem with TI is that bad actors are increasingly adept at hiding or minimizing their digital footprint and that by the time an IOC is recorded as malicious, they’ve already moved on.
Heard of avsvmcloud[.]com?
avsvmcloud[.]com was the domain used for command and control in the SUNBURST supply chain attack that compromised 18,000 victims in 2020 (when attackers inserted malicious code into SolarWinds Orion software). TI sources gave avsvmcloud[.]com a clean bill of health until the public disclosure of the hack, after which Microsoft and other companies seized the domain and sinkholed the SUNBURST malware C2.
It’s very possible that alerts for abnormal outbound communications showed up in the SOCs in at least some of the victim organizations, but analysts ignored the alerts because avsvmcloud[.]com was not flagged as malicious. This allowed the attackers to go about their business undetected for at least seven months until FireEye detected the attackers after they had stolen Mandiant’s red team tools.
While the SUNBURST attackers were highly sophisticated, this example illustrates perfectly how many organizations rely too heavily on TI sources.
How Attackers Evade Detection by Threat Intelligence Sources
Unfortunately for SOC teams, it’s getting easier for attackers to stay under the radar. First, public cloud resources make it easier than ever to create dynamic infrastructure for their campaigns so that they can constantly change IP addresses and domains. For example, AWS and other cloud service providers provide fresh pools of IP addresses, so that an attacker can use an IP address for two hours before it’s picked up by another organization. This dynamism makes it difficult for TI to catch up.
Second, threat actors are better prepared, with pools of strategically aged domains, some with considerable rankings in search engines. In the example of SUNBURST, the attackers had registered avsvmcloud[.]com two years prior.
Third, malware authoring tools check their IP addresses, domain names, and file hashes against public TI sources, including freemium offerings from vendors.
Fourth, there are a growing number of very sophisticated crimeware-as-a-service offerings that include evasion mechanisms. Evil Proxy, Naked Pages, Caffeine, and BulletProftLink are some examples of phishing-as-a-service offerings. The May 2023 Microsoft Cyber Signals report details an example of how BulletProftLink is fueling a surge in business email compromise and evading detection through dynamic infrastructure, “BulletProftLink offers a decentralized gateway design, which includes Internet Computer public blockchain nodes to host phishing and BEC sites, creating an even more sophisticated decentralized web offering that’s much harder to disrupt.”
Finally, phishing groups can use Gen AI tools to quickly and cheaply build websites that look and feel the same as target domains during domain impersonation or typosquatting attacks.
How to Fill the Gap in Your Detection Strategy
Investigating every single alert deemed “benign” by TI sources is a near-impossible task. First off, it takes a lot of time to chase down every lead and also requires a significant level of skill—beyond what a typical Tier 1 analyst could be expected to have.
If a SOC team wanted to better detect potential false negatives, one way would be to put those alerts that don’t receive TI hits into another queue and then build run books for junior analysts to follow. Given enough resources, this strategy could work, and you could justify the effort by tracking the number of false negatives caught.
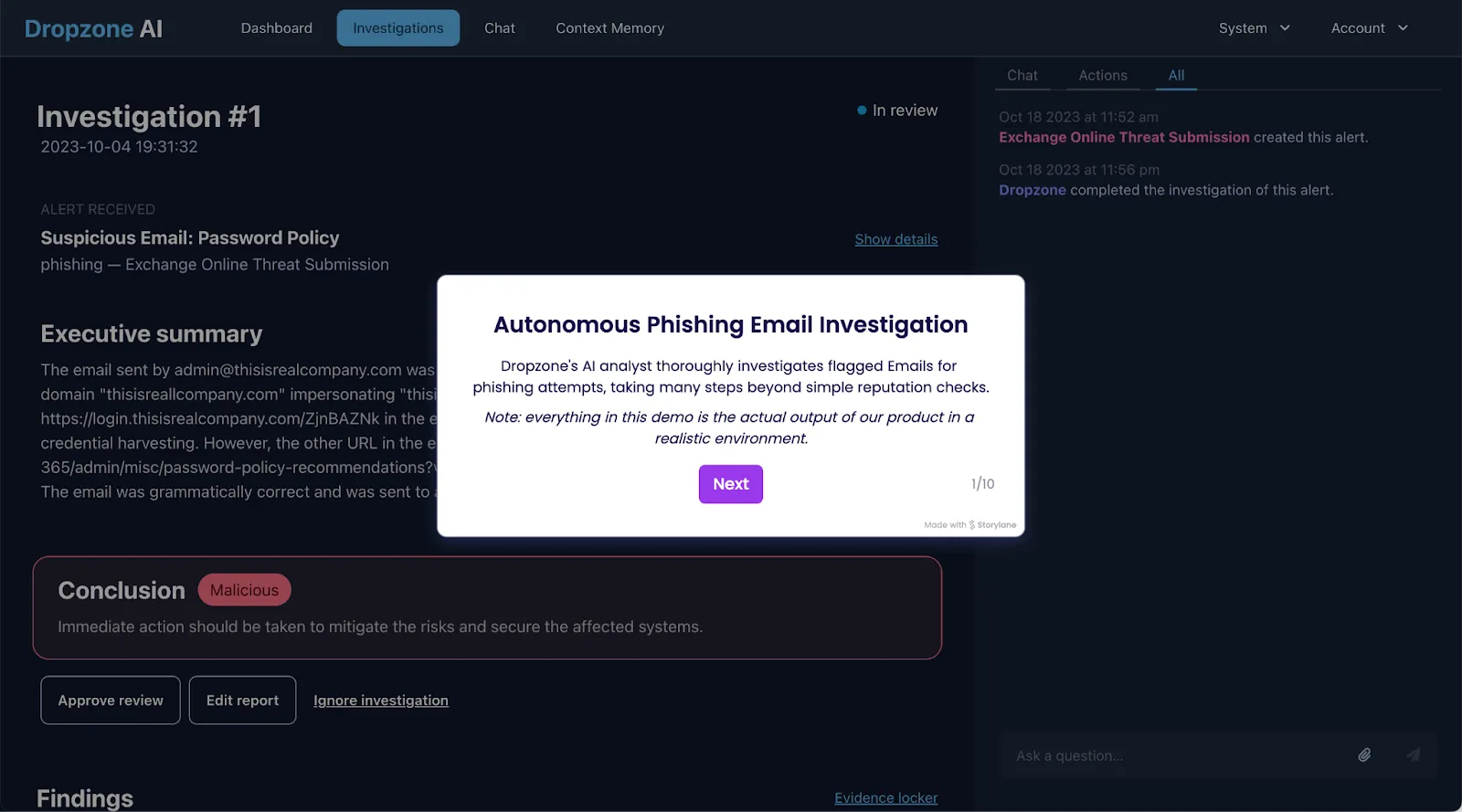
But there’s a simpler, more efficient way to reduce the number of false negatives. Recent advancements in Gen AI and LLMs have, for the first time, enabled software systems to replicate the thought processes and techniques of expert analysts. AI analysts, like what we’re developing here at Dropzone AI, can perform multi-layered investigations of every single alert to uncover malicious IP addresses and domains that are not detected by TI sources. For example, for an email with a seemingly benign URL, our LLM-driven analyst will search through past email histories to see which employees have communicated with the domain in question and check to see if the email was sent to many employees or just a few. Very often, phishing emails are sent to an individual or small group so as to not raise alarms. In the case of login pages, the Dropzone analyst will examine the target page to identify elements that are used in credential harvesting. Finally, the Dropzone analyst will compare the domain with the legitimate one and look at domain registration, IP resolved, hosts associated with the IPs, files communicated, and HTTPS certificates. Whew! That’s a lot, and would likely take a human analyst 10-20 minutes of focused effort.
A Gap in Your Defenses
More organizations are building out their detection engineering and tuning programs, significantly leveling up the effort that attackers must exert to evade detection. But when security teams excessively rely on TI sources to prioritize alerts, they have a huge potential for missed true positives. Helping your analysts to deeply investigate every alert passed by TI is challenging. While increased training and runbook development will help you get more eyeballs on the seemingly benign alerts, you can also consider augmenting your SOC with AI analysts who can thoroughly investigate every single alert, replicating hours of expert analysis.
Take a tour to see how Dropzone's AI analyst thoroughly investigates flagged emails for phishing attempts, taking many steps beyond simple reputation checks.






.png)