As security vendors race to infuse their products with AI, the SOC is being reshaped, but not always for the better. Each vendor's AI promises smarter automation, faster detection, and sharper insights. Yet in practice, every tool is becoming its own "smart island," confined to the borders of its ecosystem. Microsoft's AI copilots are familiar with Microsoft data. Endpoint AI knows endpoint data. Cloud AI knows cloud data. None of them talks to each other.
For SOC leaders, this is creating a new kind of fragmentation. The industry once struggled with too many tools and dashboards; now it faces too many isolated AIs. Each system automates within its own walled garden, unable to see or understand the full environment. The result is:
- Partial intelligence: Each AI only sees a fraction of the investigation or threat hunt
- Incomplete automation: Multiple systems each deal with part of the detection and response lifecycle, requiring humans to intervene
- AI “maintenance”: The effort that human engineers put into customizing or coaching one AI system need to be replicated across others
- No shared memory: Lessons learned in one system never reach the others
- Added noise: Disjointed assistants generate conflicting stories that analysts must reconcile
Human analysts are still left doing the stitching, connecting evidence and context that should already be unified.
What's missing isn't more AI. It's a vendor-agnostic AI layer that captures the broader perspective. One that reasons across multiple tools, understands how data interconnects, and uses both proprietary and open-source technologies as part of the same investigation or threat hunt. Instead of being trapped inside one vendor's stack, this AI acts as a bridge across them all, delivering the kind of unified intelligence that humans have always needed but machines have never provided.
What Happens When Every Security Tool Has Its Own AI?
Picture a modern SOC in action. A new alert pings in Microsoft Sentinel, enriched by Security Copilot's AI-driven insights. The analyst pivots to CrowdStrike or SentinelOne to validate whether the endpoint behavior matches the detection. Charlotte AI or Purple AI have their own story to tell. Or, it's over to Google SecOps, where Chronicle AI provides a separate layer of reasoning about network traffic.
Each of these platforms has its own AI automation, its own way of "thinking," and its own data to refer to. Yet none of them can talk to one another. The insights stop at the platform boundary. The analyst, meanwhile, is left playing the role of translator, piecing together fragments of context from tools that don't share a common language, logic, or memory.
This is the paradox of today's AI-enhanced SOC. We've automated faster, but not smarter. Each AI operates in isolation, forcing humans to bridge the gaps that machines can't see. But security analysts already move fluidly between tools, connecting evidence and context as second nature. Shouldn't their AI teammates do the same?
Is One AI per Tool Enough for Modern SOCs?
The idea of having an AI companion in every tool sounds powerful until you see it in practice. Multiple AI copilots don't form a team; they form silos. Each one sees the world through its own narrow lens, unaware of what the others are learning or deciding. There's no shared memory, no coordinated reasoning, and no consistent logic guiding their conclusions.
It's tempting to think that five AI copilots mean five times the capability. In reality, it's more like having five specialists who never compare notes, each doing their best, each missing part of the bigger picture. True intelligence isn't about having more AIs. It's about having one that can see, think, and learn across every tool your team already uses.
What Are the Risks of Single-Vendor AI Lock-In?
It's easy to see the appeal of a single-vendor AI ecosystem. The pitch is simple: buy into one stack, and you'll get seamless automation from end to end. Everything connects, everything talks, and your security operations hum along in perfect harmony.
But the reality is that very few organizations have a homogeneous security stack, with their tools all from a single vendor. Security buyers know the dangers of relying on a single vendor. The deeper your SOC embeds itself into one vendor's ecosystem, the more dependent it becomes on that vendor's rules, priorities, and pace of innovation:
- Visibility shrinks to what that stack can see
- Integration slows because automation isn't built to look beyond its own boundaries
- Flexibility disappears as your AI roadmap becomes someone else's roadmap
- Blind spots persist wherever the vendor's coverage ends
This kind of lock-in limits the one thing every SOC needs to survive: Adaptive defenses that work together no matter what path an attack takes. Attackers don't care about vendor boundaries. They move laterally across cloud, endpoint, and identity systems without distinction. To defend effectively, your AI must be just as adaptable.
What Does a Vendor-Agnostic AI Layer Look Like in the SOC?
Not another AI bolted onto a single tool, but a centralized layer that behaves like a trusted teammate rather than a collection of scripts. This type of AI doesn't reside within a single product. It lives across them all and understands how your SIEM, EDR, cloud logs, and identity systems interconnect, and it reasons through that data as one continuous investigation instead of fragmented parts.
This unified AI layer doesn't replace your tools, but rather amplifies them. Each platform remains vital for what it does best, collecting logs, detecting anomalies, or tracking assets, but the AI provides the connective tissue that ties their insights together. It pulls in evidence from every corner of the environment, correlates events, and builds a cohesive story that would otherwise take analysts hours to reconstruct manually.
Just as importantly, a vendor-agnostic AI layer remembers what it learns and applies that knowledge broadly. A centralized AI layer maintains institutional memory and recalls what's normal for your organization, how similar incidents were resolved in the past, and which systems are historically linked. That shared memory transforms each investigation or threat hunt into a smarter, faster version of the one before.
AI Should Be Fluent in Every Tool You Use
A truly capable AI SOC analyst or AI Threat Hunter doesn't pick favorites. It speaks every tool's language. In a real investigation or threat hunt, human analysts seamlessly transition between platforms: Splunk for log correlation, SentinelOne or CrowdStrike for endpoint activity, Okta for identity verification, and AWS for cloud logs. That's just the start. They might open Wireshark for packet analysis or CAPA to dissect a suspicious executable. They'll cross-check threat intelligence feeds, reputation databases, and even email systems or ticketing tools like Jira to piece together what really happened.
That's how real investigations and hunts work. Context is everywhere. And that's exactly how your AI should operate. It should be able to query identity systems such as Microsoft Entra ID to understand permissions, reference Google Workspace or Microsoft 365 to verify legitimate communications, and pull business data alongside threat data to build a comprehensive picture. This isn't just about integrating more APIs. It's about reasoning across them naturally, just as a human would.
To do that effectively, your AI layer must normalize information without flattening it. The nuance of a log from Splunk isn't the same as an IAM permission in AWS, and both hold critical details that shape the outcome of an investigation. A strong AI layer preserves that richness while connecting the dots, applying logic instead of relying on rigid playbooks.
The most valuable AI is the one that treats every tool as a first-class citizen, whether commercial, open source, or homegrown. It moves fluidly between them, understands their context, and uses each one for what it does best.
Unified Reasoning Across the Stack
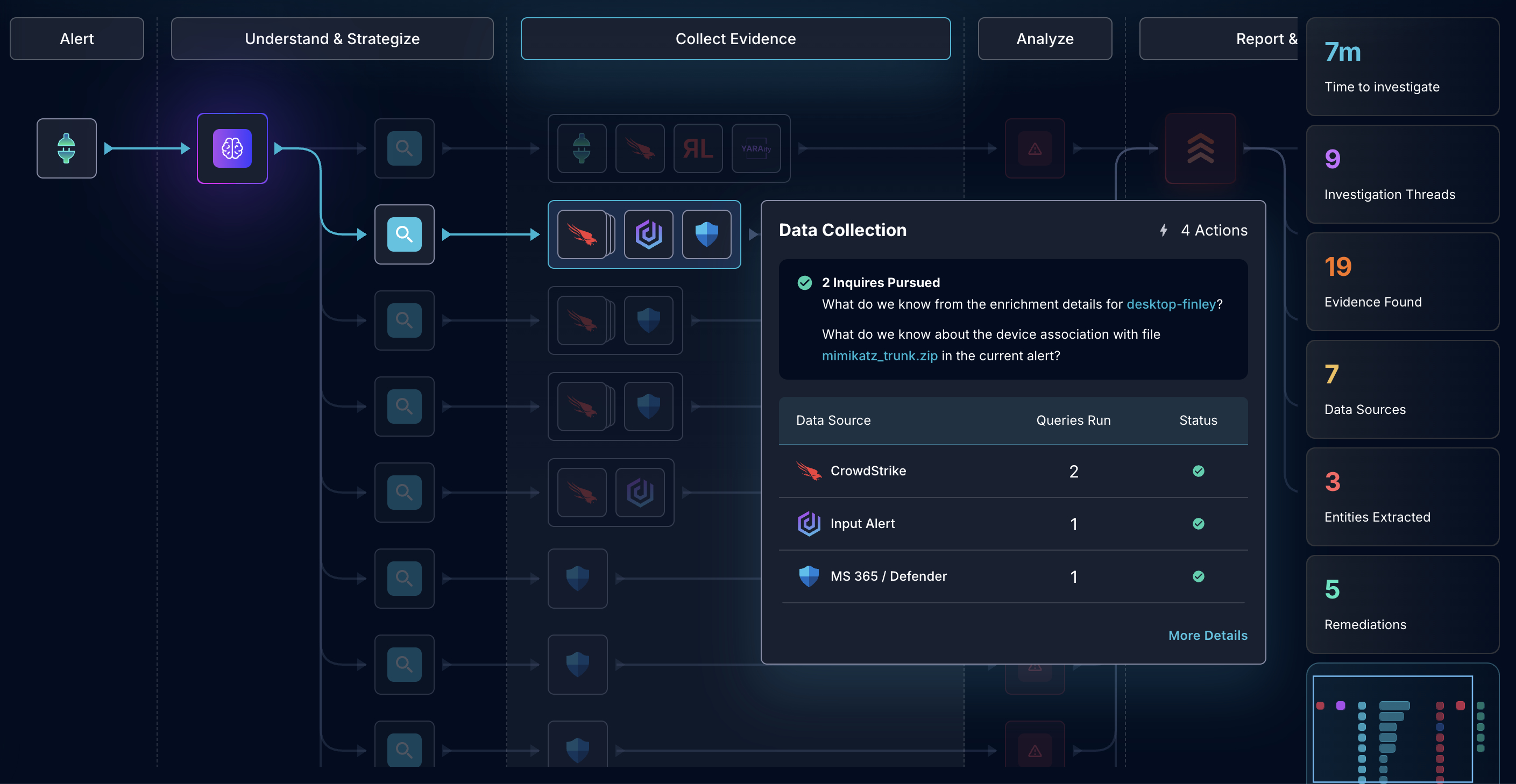
Here's where the story comes together. Dropzone AI is the vendor-agnostic layer your SOC has been missing. It’s AI SOC Analyst, AI Threat Intel Analyst, and AI Threat Hunter don't live inside a single product. They sit above the stack and work across it. When an alert fires or a hunt pack arrives, Dropzone pulls evidence from your SIEM, checks endpoint telemetry, consults cloud and identity logs, and adds business context from the systems your teams actually use. One investigation or hunt. One narrative. All the tools you already trust.
There are no playbooks or brittle scripts to maintain. For investigations, Dropzone plans and replans its next step using autonomous, recursive reasoning. It tests a hypothesis, gathers evidence, and adjusts its approach based on what it finds. That means fewer dead ends and faster clarity. For hunts, Dropzone can pull millions of rows of telemetry from your tools, boil them down to a handful of anomalies, and chase those leads down using all the tools that your human analysts do.
The payoff shows up in the day-to-day:
- Consistent logic across tools: Conclusions no longer contradict each other because a single reasoning engine evaluates all the evidence
- Shared memory across cases: Lessons from one alert carry forward, so the system gets sharper over time
- Federated hunts that are vendor agnostic: Agents use all the tools that you have deployed to chase down every lead
- Unified audit trail: Every case produces a clean investigation summary, ready for review or handoff
In short, Dropzone doesn't care which tools you use. It makes them all smarter.
Why Should Your AI Work the Way Your Analysts Already Do?
The distinction between tool-specific AI and vendor-agnostic AI comes down to the difference between assistance and transformation. Tool-specific AI helps within its lane. It can summarize, analyze, or automate within one platform. But security investigations don't happen on a single platform. Analysts constantly move between tools, connecting endpoint data to identity logs, matching SIEM alerts to cloud events, and validating findings against business systems.
Your AI should work the same way. A modern SOC doesn't need five disconnected copilots arguing over the same alert. It needs one teammate who can see the entire threat surface, think across every system, and build a complete, cohesive understanding of what's happening. Unified AI is more than automation. It's reasoning that mirrors how your best analysts already operate. That's what Dropzone delivers. It's not another tool in the stack but a teammate that works with whatever you already have.
Want to see how Dropzone works with the tools you already have? Explore our self-guided demo and see how it expertly uses tools from multiple vendors.







.png)