I started Dropzone AI three months after OpenAI released the public beta of ChatGPT in November 2022. I saw what LLMs could do and knew immediately that this technology could add much-needed cognitive capacity to the SOC.
Today, I want to share what we've learned and where we're going. We're announcing two new agents joining the Dropzone team: AI Threat Hunter and AI Threat Intel Analyst, both of which are currently in testing with beta customers and will be generally available this summer. But this post isn't just about new products. It's about the product philosophy behind them, why we waited until now to expand the team, and why the choices we've made will matter more as this market matures.
What's Changed Since We Started Building the Agentic SOC?
At the beginning of 2023, the idea of an AI agent that could investigate a security alert end-to-end sounded ambitious, to say the least. Three years later, our AI SOC Analyst is deployed at more than 300 organizations, investigating alerts around the clock, with the consistent depth and rigor that a senior analyst would apply.
We first coined the term "AI SOC Analyst," and now it's everywhere. Gartner recognized the category in its 2025 Hype Cycle for Security Operations, naming Dropzone AI a sample vendor for AI SOC agents. Competitors adopted the language. The concept isn't new anymore.
But while a single AI SOC analyst is immensely valuable, we know that much more is possible. We’ve only begun to scratch the surface of what LLMs can do to help SOCs adapt and respond to increasingly AI-driven attacks. That’s why our new AI Threat Intel Analyst and AI Threat Hunter are built to collaborate with each other and with the AI SOC Analyst. They’re a team of agents that executes human strategy round the clock, at machine scale.
Why Now? AI Is Changing Both Sides of the Fight
The Agentic SOC vision that we’re pursuing meets an urgent need. Anthropic's Frontier Red Team published findings this year showing that AI models can now discover real zero-day vulnerabilities, write working exploits, and execute multistage attacks across networks with dozens of hosts using standard tools. In one collaboration with Mozilla, Anthropic’s Claude model found 22 previously unknown Firefox vulnerabilities in two weeks.
Increasingly, attackers are less constrained by skill or time, and more by the inference tokens they can afford.
On the defensive side, most SOCs are still fundamentally operating the same way they did five years ago. The agentic SOC model is the only way to keep pace. That's why we're expanding the Dropzone agent team now.
Why Does 100% Software Matter?
Every Dropzone AI agent is 100% software. No offshore analysts reviewing escalations behind the scenes. Some vendors use low-cost human analysts to touch up what their AI produces. You could call this "artificial artificial intelligence." And while it does work at a small scale, it doesn't work when you have 10,000 customers. You can't hire your way to consistency, and you can't scale a service that depends on human review for every edge case.
Our approach is different. We build AI agents that execute consistently, with zero variance between the 3 AM shift and the Monday morning shift. Every investigation is fully transparent: every tool queried, every reasoning step exposed, every decision traceable.
The human role in this model is strategic, and it breaks down into three parts:
- Scope of work. You decide which alert types the agents investigate, which hunts they run, and how frequently. The agents execute; you set the priorities.
- Authorization. You control what systems agents can access and their level of privilege, whether they can interview users, and when they're allowed to take automated containment actions.
- Context. You give agents the knowledge they need about your business, your operations, your environment, and your policies. This tribal knowledge is shared across agents.
This is how the agentic SOC will execute your strategy at machine scale.
How Do the New Agents Work Together?
Dropzone is known for our AI SOC Analyst. We selected threat intel analysis and threat hunting as the next disciplines to tackle because of the synergies that the three agents bring when working together.
Here’s an all-to-common scenario that these agents can solve: A critical zero-day is discovered in an ubiquitous open-source library on Sunday night along with reports that an exploit is in the wild. Normally, you’d arrive on Monday morning to dozens of unread Slack messages asking about your exposure. Are we compromised? Do we see signs of exploitation attempts? What about past exploit attempts before the zero-day vulnerability was announced?
This is why you need a team of AI agents working round the clock to help you adapt and respond.
AI Threat Intel Analyst monitors hundreds of threat sources, tracks relevant TTPs and IOCs for your industry, and creates hunt packs for emerging threats. When it detects a new CVE or a trending attacker campaign, it automatically builds a hunt pack containing various behavioral signatures and hands it directly to the AI Threat Hunter.
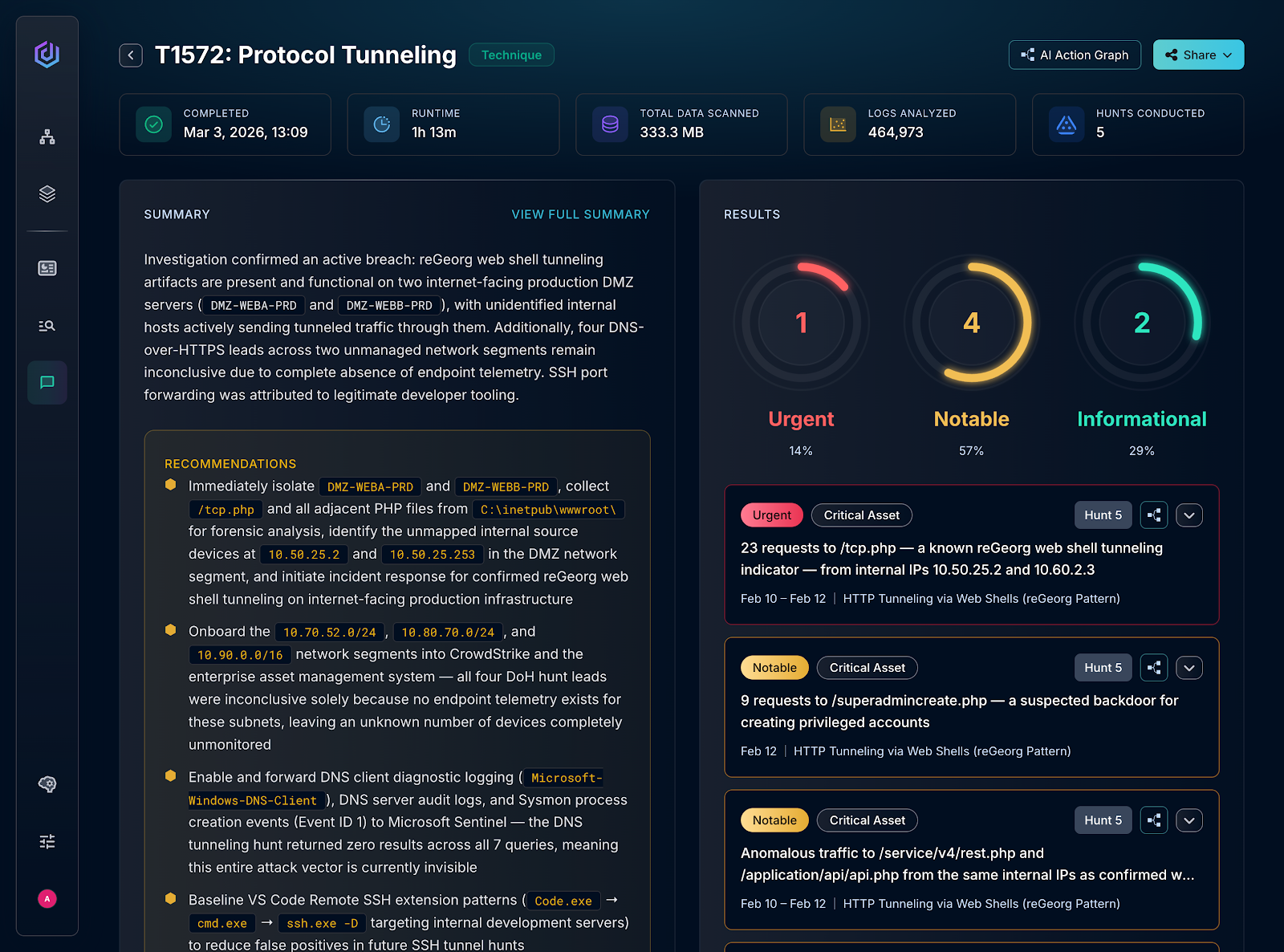
AI Threat Hunter executes hypothesis-driven, federated threat hunts across your SIEM, EDR, and cloud tools:
- 250+ pre-built hunt packs, including coverage for every MITRE ATT&CK technique
- Custom hunting objectives on demand, described in natural language
- Compresses up to 40 hours of human analyst work into roughly an hour of agent work
- Vendor-agnostic across Microsoft Sentinel, Splunk ES, CrowdStrike, and any connected platform
As Andrew Marsh, Director of Information Security at Indiana Farm Bureau Insurance, put it: "Dropzone's AI Threat Hunter performs federated hunts in 1 hour that would take humans up to 40 hours."
These agents work together without anyone telling them to.
So, getting back to our zero-day vulnerability announced on Sunday night:
- AI Threat Intel Analyst detects an emerging threat and builds a hunt pack
- AI Threat Hunter runs the hunt across your entire stack
- AI SOC Analyst investigates unexplainable anomalies found in your environment and delivers a complete report
- Monday morning, your team walks in to a finished hunt report with findings, evidence, and recommended actions
No human initiated any of that. You gave the agents the scope of work and the authorization and they did the rest. That closed loop is the real differentiator. In the agentic SOC, agents autonomously task each other, share context, and compound capability as the team grows.






