Introduction
The year is 2030. You walk in on a Monday morning to a zero-day vulnerability that dropped Sunday night. A few years ago, that meant a scramble: Pull the team in, query the SIEM and other systems, figure out exposure, and brief the CISO, all before touching the alert queue. Today, you open Dropzone AI and the work is already completed for you. The AI Threat Intel Analyst saw the advisory overnight, extracted TTPs and built a hunt pack, and passed it to the AI Threat Hunter. Ninety minutes of federated searches across your SIEM, EDR, and cloud. A 30-day lookback. 464,000 events narrowed to nine findings, each one investigated and classified. When your CISO asks if you're exposed, you already have the answer.
Here's what the rest of the day looks like when your AI agents handle the frontline, and you focus on the work that actually needs you.
How Does an Agentic SOC Handle a Zero-Day Vulnerability Before You Arrive?
While you were sleeping, the AI Threat Intel Analyst had already seen the overnight advisory, extracted TTPs and built a hunt pack, and handed it to the AI Threat Hunter, which ran federated searches and delivered classified findings before your first coffee.

What Happened While You Were Sleeping?
While you were offline Sunday evening, the AI Threat Intel Analyst was reading the same advisory your peers were sharing in group chats. It extracted the relevant IOCs and TTPs, matched them against your technology stack, and automatically built a hunt pack.
That pack went straight to the AI Threat Hunter, which kicked off federated searches across your SIEM, EDR, and cloud platforms. Over the next 90 minutes, it queried and processed hundreds of thousands of telemetry rows with a 30-day lookback, searching for any sign that this vulnerability had been exploited in your environment before anyone knew it existed.
By the time you sit down on Monday morning, the hunt is finished. 464,000 events narrowed to nine unexplained anomalies, each one with a full investigation, gathered evidence, documented reasoning, and a clear classification. You scroll through the report. Two findings stood out as notable: a misconfigured test server that would have been vulnerable, and a patch gap on three endpoints that need attention. Thankfully, no signs of active or past exploitation attempts. You know exactly where you stand and what needs fixing.
What Used to Cause a Monday Morning Scramble?
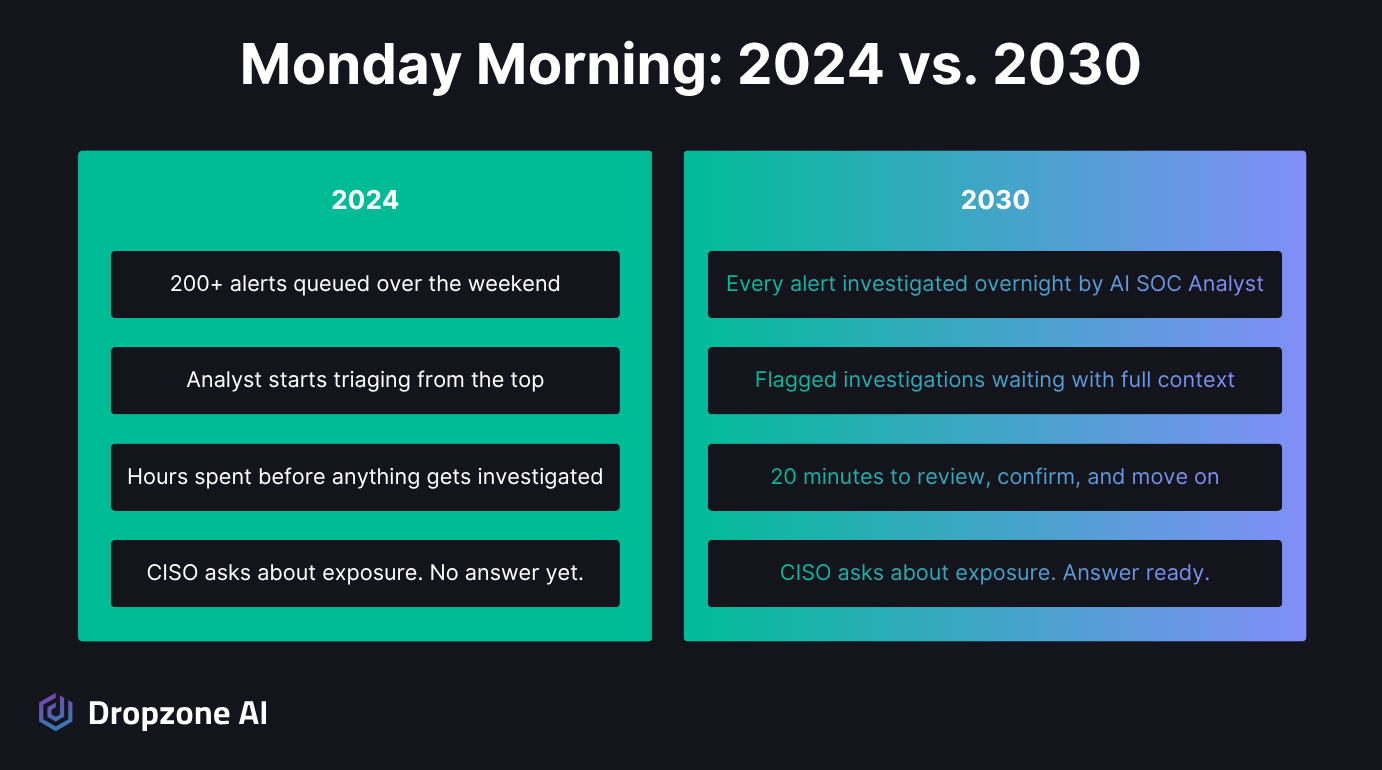
Right on schedule, the CISO pings the security channel. "Are we exposed to the new zero-day?" In 2024, that question would have kicked off hours of work: Manually querying across tools, cross-referencing asset inventories, chasing down system owners, pulling analysts off whatever they were working on, and hoping nothing slipped through the cracks. The answer would come eventually, but it would cost you most of the morning and leave most of the SOC’s alert queue untouched.
Today, you attach the Dropzone hunt report into the thread with your own commentary and move on with your day. The report contains clear findings, documented evidence, and specific remediation steps for the two items that need attention.
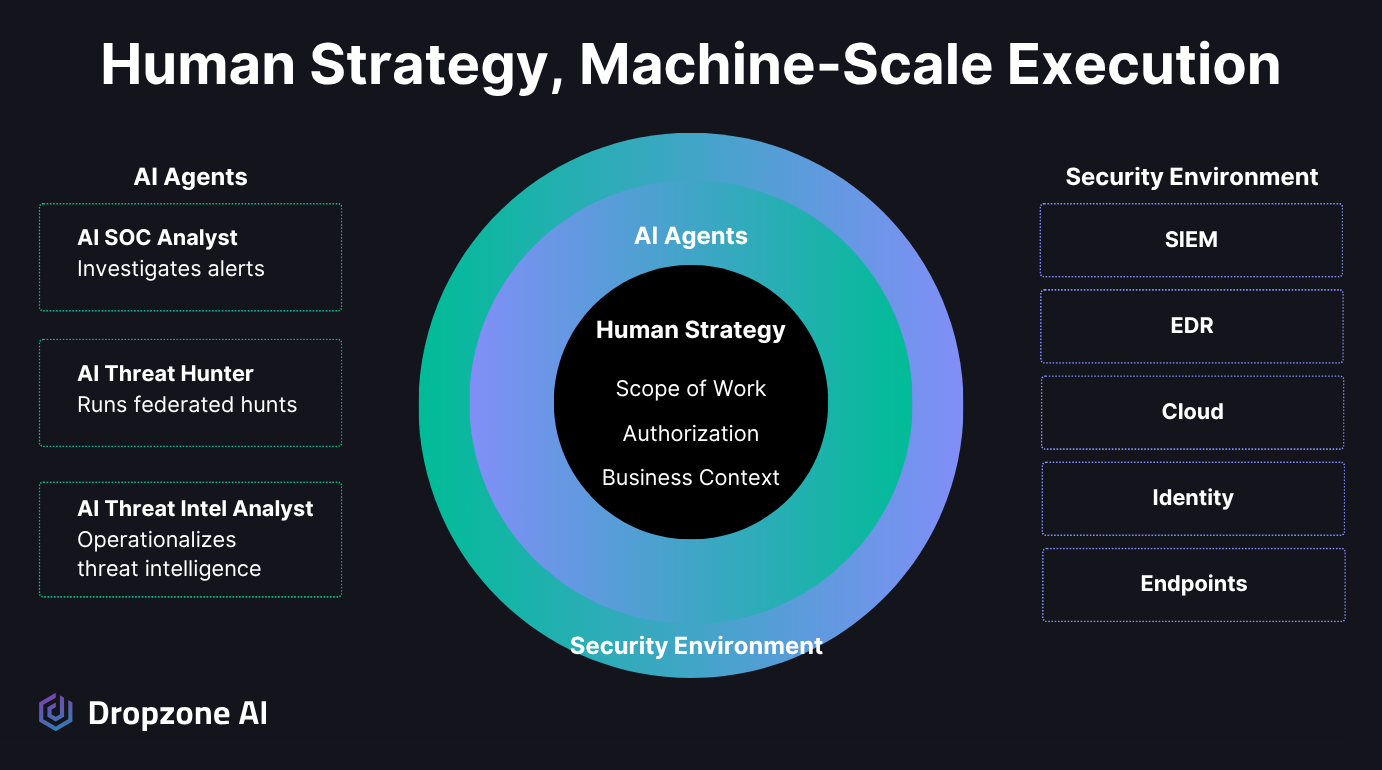
That's the AI Threat Hunter and TI Analyst working together in the background, the way they're designed to. They execute your human strategy. You set the hunting priorities and authorization boundaries. They execute continuously, whether it's a Tuesday afternoon or a Sunday night. The zero-day didn't wait for business hours, and neither did your agents.
What Does Monday Morning Actually Look Like Now?
Unlike in the past, your Dropzone AI SOC Analyst has already triaged and investigated the entire SOC alert queue. You spend 20 minutes on the handful of alerts that need a human judgement call, then move to the work that actually needs you: project planning, cloud engineering alignment, and calls with vendors.
How Are the Alerts Already Handled?
The zero-day wasn't the only thing that happened over the weekend. Alerts kept coming in the way they always do, and the AI SOC Analyst handled all of them while you were gone. Every alert got a full investigation, not just a triage label.
The AI pulled context from across your stack, gathered evidence, documented its reasoning, and reached a conclusion. The ones that need human attention are waiting with everything you need to make a call. Actual malicious activity received an appropriate automated response, according to the response actions that you authorized the AI agent to take in those situations: suspending an account, revoking session keys, or blocking IPs.
You spend about 20 minutes reviewing the investigations that are marked as malicious and suspicious, confirming a few conclusions, adjusting one where you have context the AI didn't, and adding a note to context memory so it handles that pattern better next time.
What Work Actually Needs a Human?
The rest of your Monday looks nothing like it would have five years ago. The morning is a tabletop exercise with the rest of the incident response team. You're simulating a supply chain compromise scenario, and you pull from recent hunt reports to build a realistic attack narrative grounded in actual TTPs the AI Threat Hunter flagged in your environment last month. The exercise is sharper because the threat data is real, not hypothetical.
Midday, you're in a meeting with the cloud engineering team. They're standing up a new AWS environment for a product launch next quarter, and your job is to define what Dropzone should monitor, set the authorization boundaries for automated containment, and add the relevant business context to context memory so the AI SOC Analyst understands what normal looks like in this new environment from day one. After lunch, you review custom strategies based on the last month of investigation data.
A couple of alert categories are performing consistently well, so you expand the AI's scope to cover them fully. One internal dev tool has been generating false positives, so you add a context memory entry to fix it.
Late afternoon, you're evaluating a new proprietary threat intel feed and mapping out how to integrate it with the existing hunt packs. None of this work is reactive. All of it scheduled strategic work that is making your organization more secure.
What Is the Human Role in the Agentic SOC?
Your role shifts from frontline triage to direction. You manage three levers daily, scope of work, authorization, and business context, and those levers decide what the AI agents focus on, what they're allowed to do, and what they know about your environment.
Why Does Strategy Replace Triage?
Now the work is what drew you to security in the first place. You're thinking about your organization's threat model, planning how to improve defenses, collaborating with teams across the company, and translating what you know about the threat landscape into concrete changes to your environment's protection.
The three levers you manage every day—scope of work, authorization, and business context—aren't something you configured once during onboarding. They're the ongoing job of directing your AI SOC agent team. You're constantly refining what the AI agents focus on, what they're authorized to do, and what they know about your environment. That's the work that makes the whole system better over time, and it's work that a human does best.
Why Don't the Agents Clock Out?
You head home around 6 p.m. The AI SOC agents don't. Overnight, they'll keep investigating alerts as they come in, running scheduled hunts, and analyzing to new intelligence as it surfaces. If news of a new campaign that affects your industry drops at midnight, the TI Analyst will pick it up and build a hunt pack from the TTPs it extracts from the reports.
If a critical alert fires at 3 a.m., the AI SOC Analyst will investigate it thoroughly, and will trigger response actions within the authorization boundaries your team sets. If it's something that needs a human call, a complete investigation report with all the evidence and reasoning will be waiting when someone opens their laptop in the morning.
That's the Agentic SOC, not a system that replaces your team, but one that expands what the same team can cover. AI handles the volume, the speed, the 3 a.m. alerts, the weekend queues, and the tedious cross-referencing across six different tools. Humans handle the direction. And tomorrow morning, you'll walk in, coffee in hand, and the work will already be done.
Conclusion
The AI SOC Analyst described in this story is generally available today. The AI Threat Hunter and AI Threat Intel Analyst were announced in March 2026 and will be generally available in Summer 2026. In addition, Dropzone is planning additional AI SOC agents that will collaborate to tune detections, harden configurations, fix visibility gaps, and assess damage from incidents. Want to see how these agents work together? The self-guided demo lets you explore a live Dropzone environment on your own.






