Cloud computing has revolutionized how businesses operate today, offering unparalleled scalability, agility, and cost savings. However, the cloud brings its own security challenges for the security and operations (SOC) team by expanding the attack surface and increasing complexity. This article explores SOC teams' challenges in investigating cloud security alerts, applying generative AI to cloud alert investigations, and offers a step-by-step look into how Dropzone AI analysts investigate autonomously with a real-world cloud event example.
Challenges of investigating cloud security alerts
80% of enterprises report having experienced at least one major cloud-related security incident. These incidents stem from internal and external actors. Internal factors include misconfigurations or human error that unintentionally expose data. External actors use malware and botnets or exploit API vulnerabilities to infiltrate and steal information, hold ransom, or mine cryptocurrency. This threat is exacerbated by the potential for adversaries to use AI and automate tasks such as vulnerability scanning, finding security flaws in infrastructure, or developing malware and bots that mimic legitimate traffic.
If you are a security analyst, you know the challenges of investigating and securing the cloud.
- Visibility: Cloud environments often have less visibility and control compared to on-premise environments. While Cloud Service Providers (CSPs) offer cloud visibility solutions such as AWS Cloudwatch, they are limited to knowing what’s happening within their cloud environments. CSPs also limit what you can see and monitor, so organizations rely on third-party monitoring tools for custom data pulls. That adds to analysts' growing list of tools to dig into to get the complete picture.
- Volume, variety, and vague alerts: Cloud environments generate a lot of alerts due to the scale and automated nature of cloud environments. These alerts lack critical information to assess the severity readily. For example, a real-time S3 alert fired would lack details such as user involvement in API calls, the timing of API calls, and unauthorized access attempts. In addition, each cloud platform comes with its diverse set of services. This means diverse datasets, analytics, and logs to parse through, consuming valuable time and resources.
- Integration of security tools: Cloud environments are complex, resulting in complex integration with security tools. These integrations add more noise to an already noisy cloud environment.
- Skillset and training: Investigating properly in a cloud environment requires a vast amount of knowledge. Training individuals on cloud security is hard. There are not enough people to investigate alerts compared to the amount of alerts generated.
With this compounding complexity, it is no surprise that it takes an average of 6 days to resolve a cloud-based alert. Such delays can significantly impede timely security response in a world rife with cloud-based threats and threat actors rapidly weaponizing AI to launch attacks. Security automation using Gen AI to conduct investigations rapidly can turn the table around and give your SOC team an upper hand.
Gen AI can be trained to triage and analyze security alerts and mimic human reasoning to identify threats and filter out noise. These systems can work tirelessly 24x7, ensuring no threat goes unnoticed at a faster pace and freeing up human analysts for critical tasks.
Security automation and autonomous alert investigations with Dropzone AI
Dropzone AI augments your SOC with AI analysts that can thoroughly and autonomously investigate every single alert at machine speed. The AI analysts replicate expert human analysts’ decision-making process, understand your team and company’s context, and adapt to an ever-changing threat landscape to investigate all alerts. As part of the autonomous alert investigation, our system swivel-chairs and collects data from your CSP’s APIs and other security data sources, such as network logs and threat intel, conducts inquiries through an AI chatbot, and gathers context to perform detailed analysis. No playbook or code deployment is needed.
While SOAR automation can quickly break in a cloud environment as the complexity and volume of alerts increase, Dropzone AI employs recursive reasoning, pushing the analysis beyond if-then analysis and data enrichment. It can also recognize unusual patterns and unknown threats to definitively conclude whether an event is malicious.
Key factors influencing the effectiveness of AI-based investigations
The following key criteria drive Dropzone AI’s unique ability to conduct effective autonomous investigations with precision:
- Pre-training: Our AI systems are pre-trained and, as a result, know how to investigate alerts from day one of deployment rather than having to learn from human analysts after deployment.
- Extensive integrations with existing security tools: Dropzone seamlessly integrates with customers’ existing tools so it can tap into organization-specific data, understand context, and conclude with improved precision.
- Human-in-the-loop: Dropzone is built with a human-in-the-loop mindset. Transparency is key. Every single action, investigation, and deduction is traceable to real data, not black box algorithms. The system is able to prove its recommendations in the form of a detailed report with severity conclusion, executive summaries, and key evidence, instilling confidence that it isn’t hallucinating.
Investigating cloud security alert with Dropzone AI: A real-life example
The section below shows in detail how Dropzone AI conducts a thorough end-to-end investigation of a real-world Okta Threat Insight alert emulating the thought process of an expert SOC analyst.
In this example, AWS GuardDuty has fired an alert and sent it to Splunk. It looks like an exfiltration attempt where a user has downloaded a lot of data from an S3 bucket.
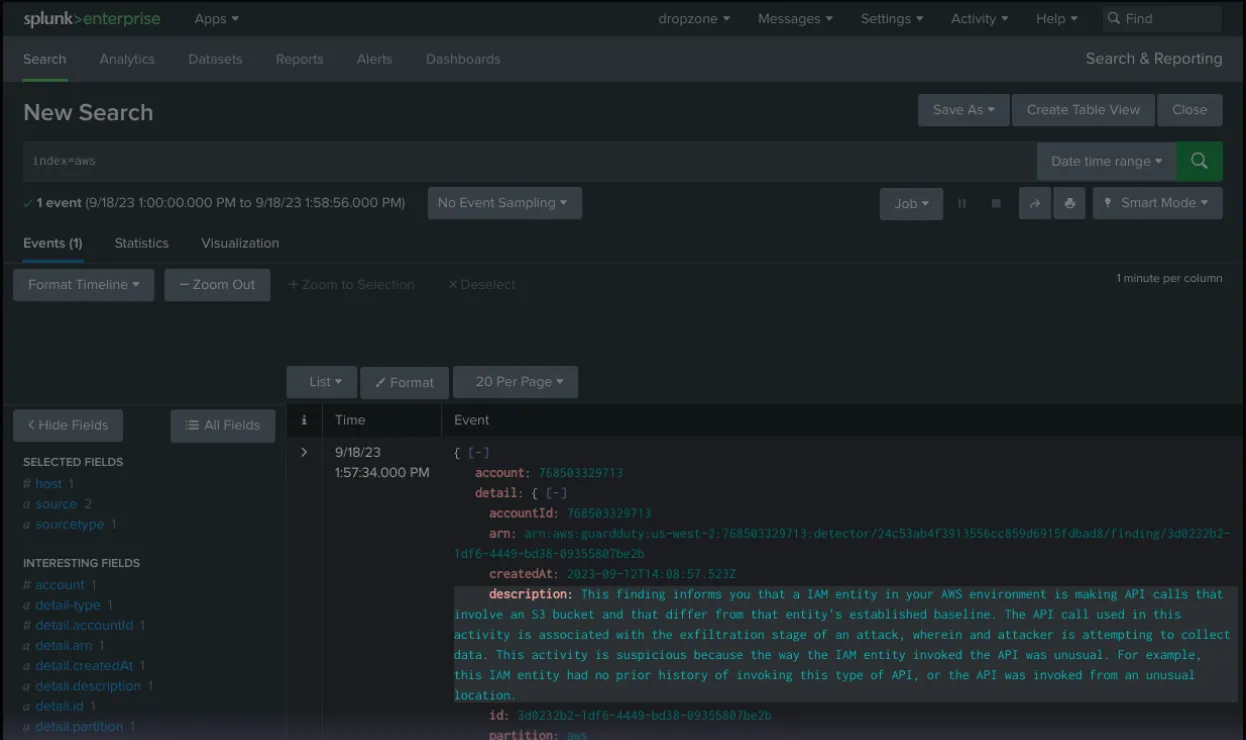
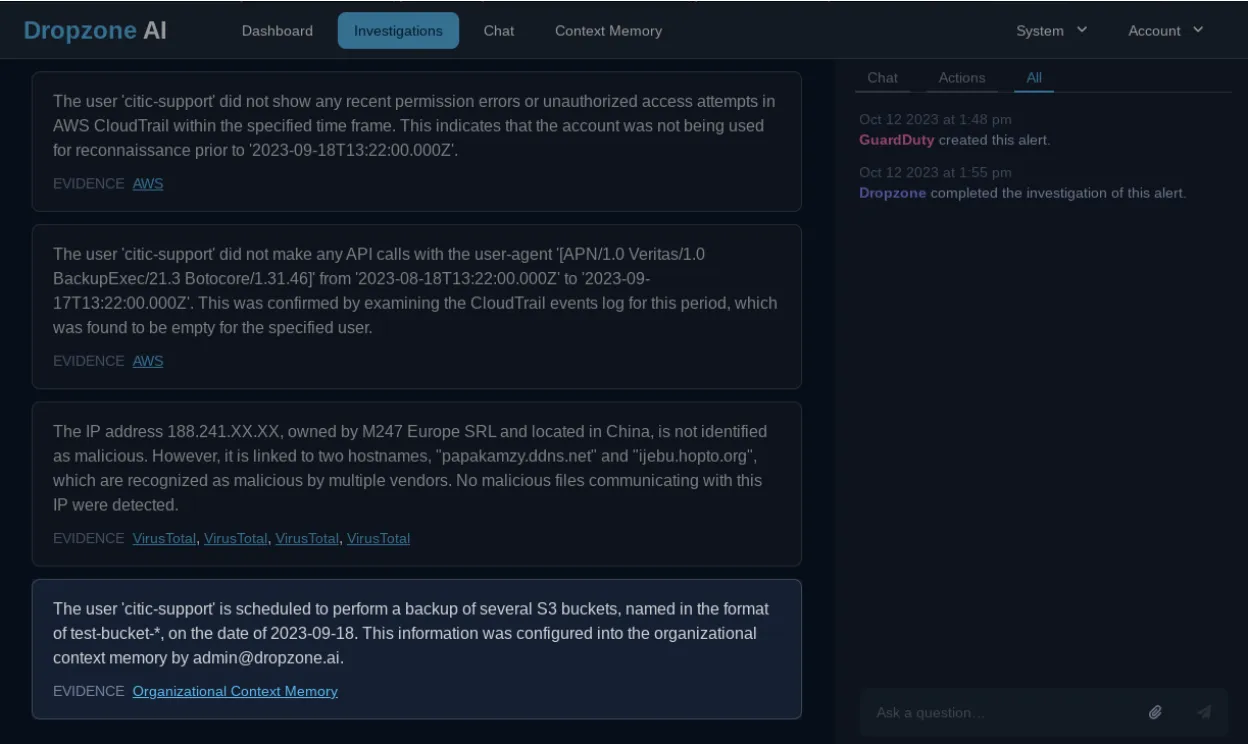
Integrated seamlessly into Splunk, before any human analyst could pick it up, a Dropzone AI analyst picked it up, conducted a thorough analysis, and determined that it was a false alert in a few minutes.
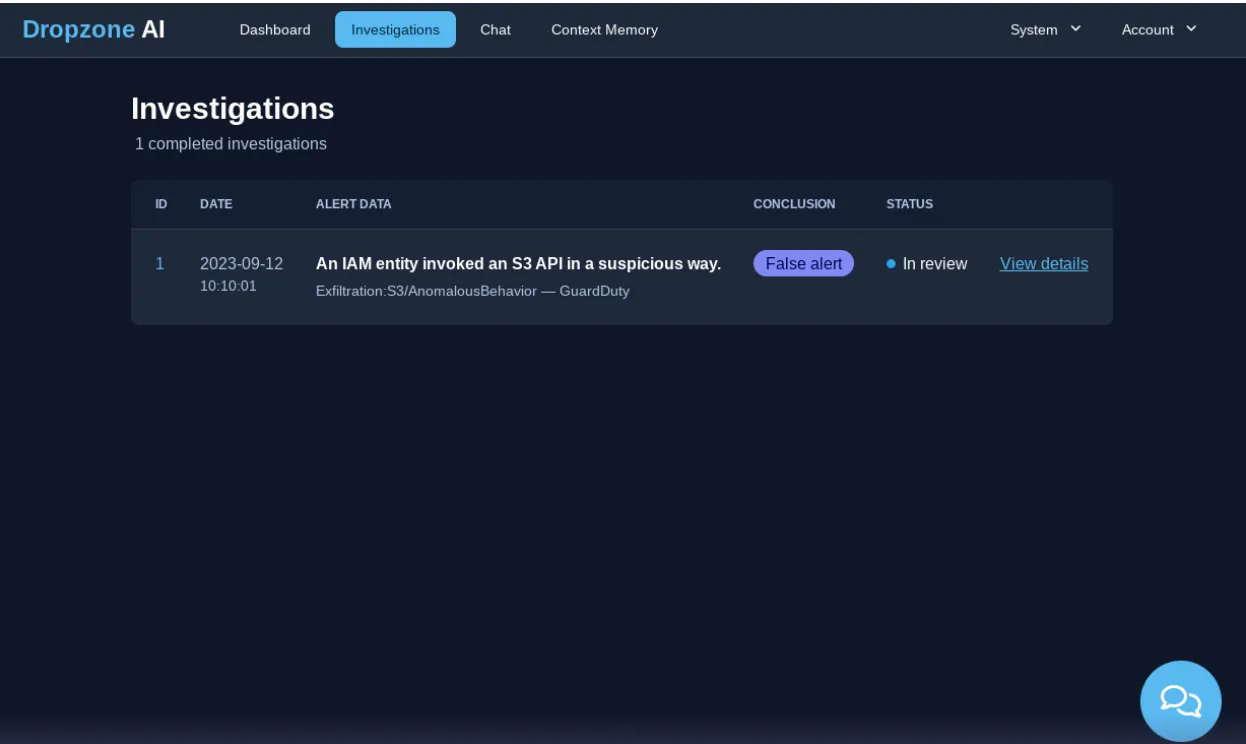
The system then generated a comprehensive report with a conclusion, executive summary, step-by-step process, and key factors used to arrive at the conclusion that it is a false positive.
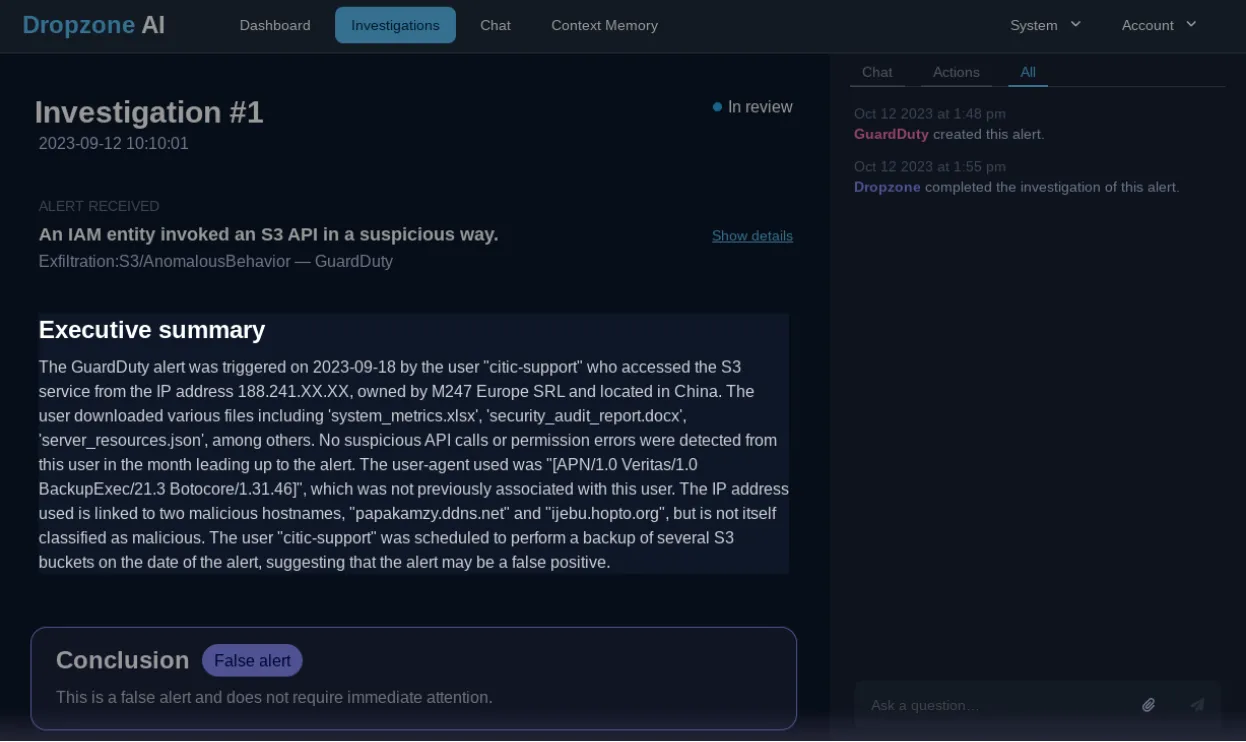
To perform this analysis, the system programmatically generated SQL queries against the AWS CloudTrail datastore to retrieve the information needed for the investigation. It identified the user and the files downloaded by the user from S3 buckets.
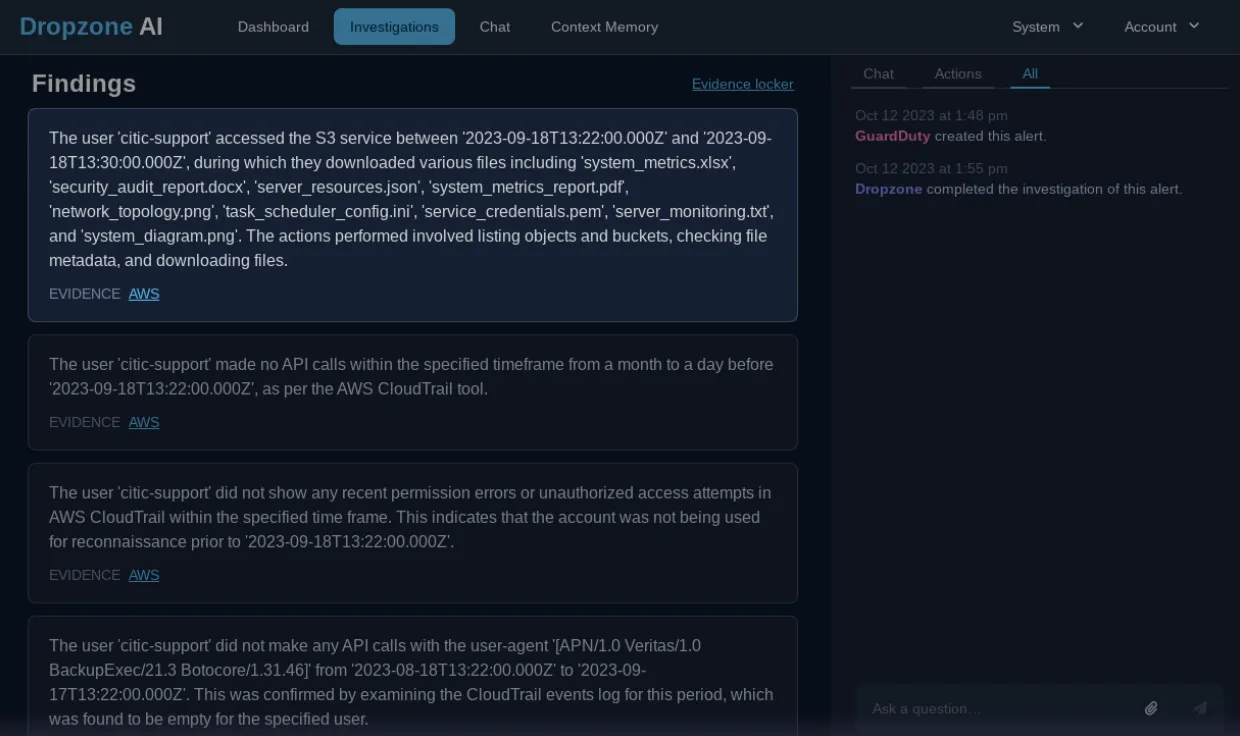
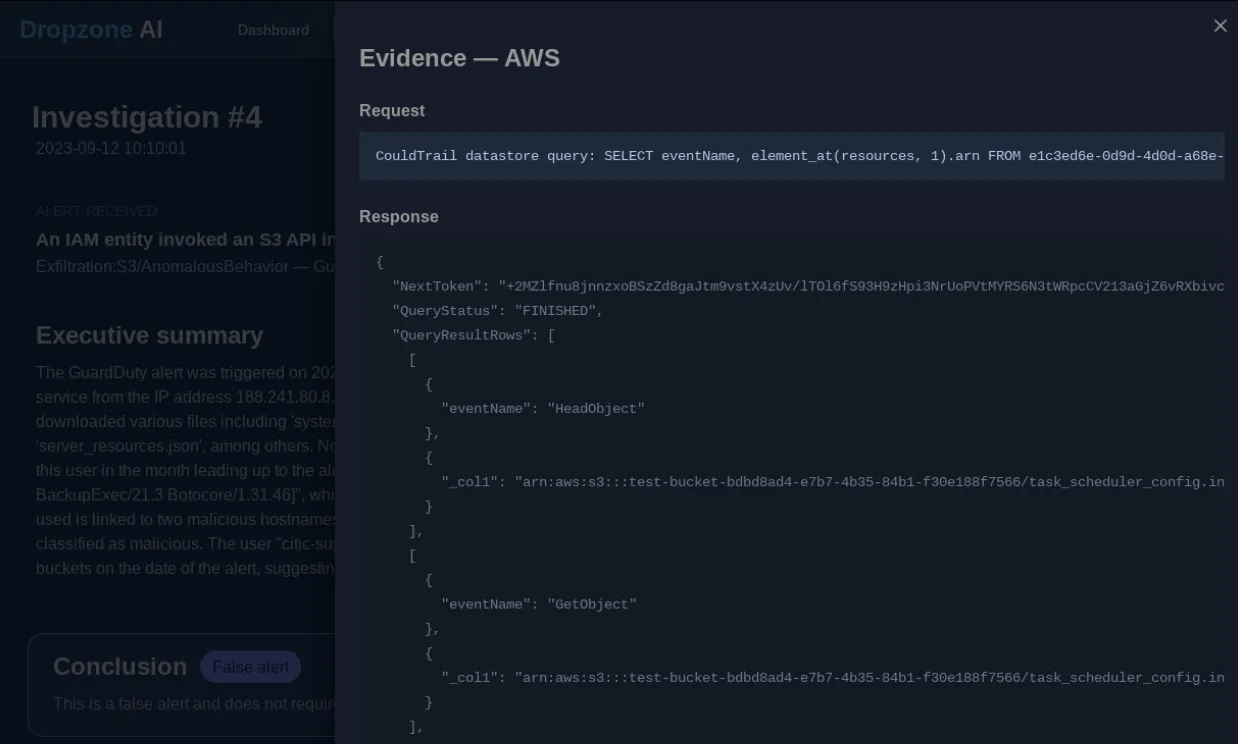
Raw outputs from relevant data sources are recorded as immutable evidence so human analysts can quickly validate the AI reasoning.
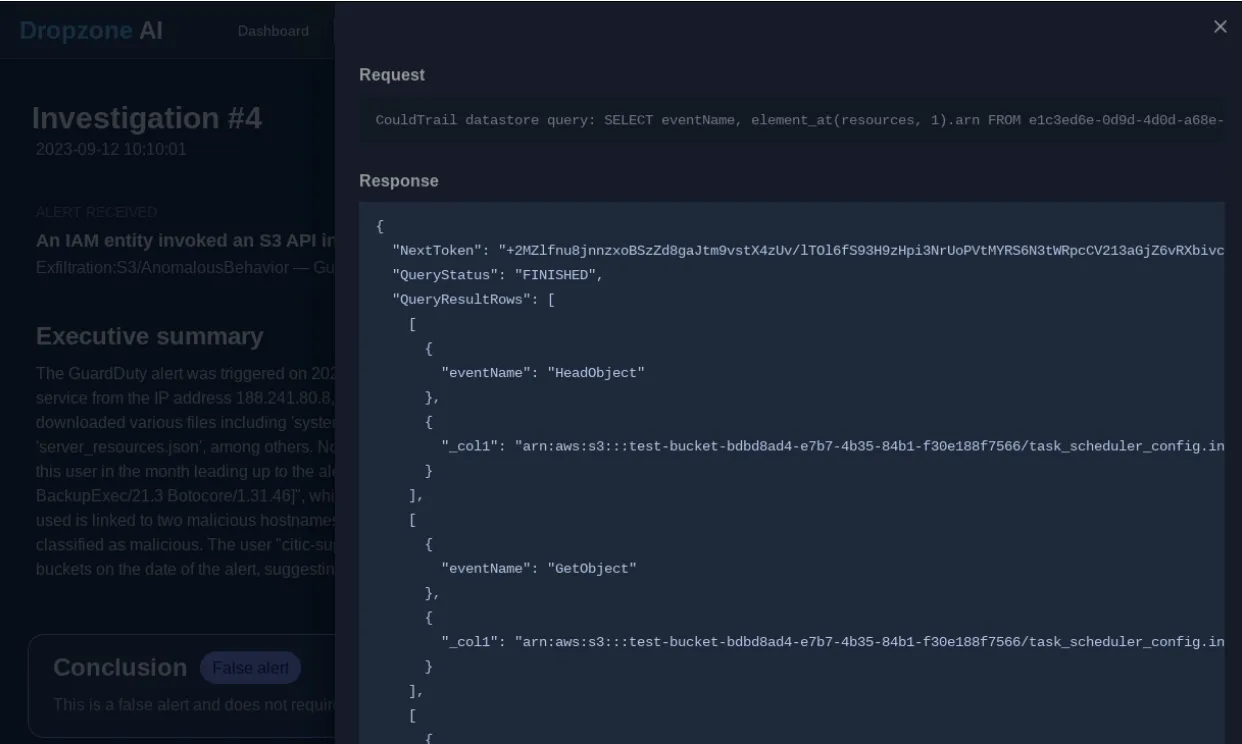
Examining AWS CloudTrail event logs, it found evidence that the user did not make any API calls before this event.
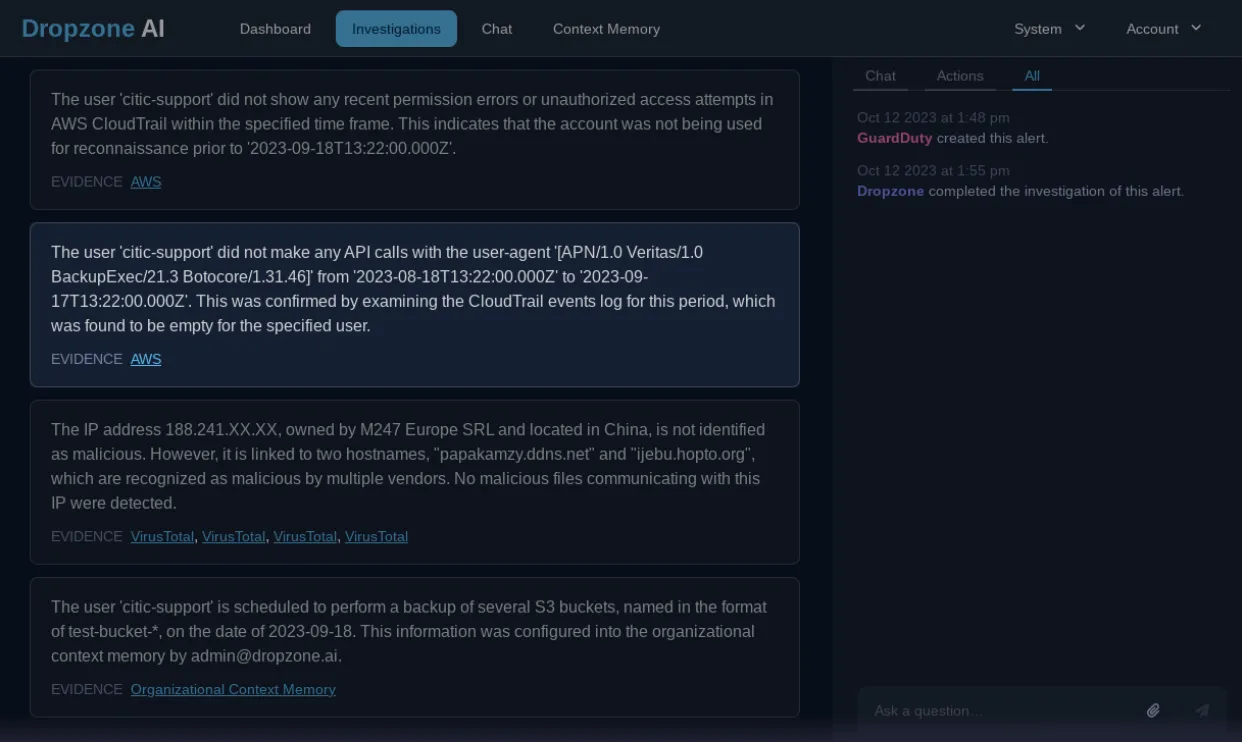
It concluded by identifying that a scheduled backup on the relevant S3 bucket caused this alert utilizing the institutional knowledge that the system had automatically learned from past tickets and existing documentation configured into Dropzone’s context memory.
All of this is 100% machine-led, whereas a manual investigation would have required a human analyst to mine data from disparate consoles with frequent context switching and then perform a manual analysis.
Reduce MTTR without stretching your SOC team
Security automation with Gen AI can help strengthen cloud security by triaging alerts faster and spotting real threats quicker and at scale. Reinforce your SOC with Dropzone AI security automation. No playbooks, no manual interventions. Request a demo or take a test drive today!
.webp)






