Key Takeaways
- By 2030, the day-to-day work of a SOC analyst shifts from running investigations to operating the AI agents that run them instead. Humans set the scope of work, authorization, and business context, and the agents act accordingly.
- The order of qualifications in job descriptions for human analysts flips. Clear written communication, AI literacy, and systems thinking move to the top of the list, while SIEM expertise and certifications move down into supporting auditing skills.
- Team headcount stays roughly the same; the team's shape changes. Senior analysts recover the strategic work they were supposed to be doing all along, and a new agent-tuning role emerges once configuring the agent layer becomes too big for one operator to handle on the side.
Introduction
Thursday night, 2030. The office is quiet except for the cleaning crew. A SOC manager opens the careers page to draft four new postings before Friday's review.
On a whim, he opens his archive and finds the job description (JD) he answered when he applied here in 2026. The work it describes barely exists anymore. Before he writes the new ones, he wants to sit with what has changed.
For the broader view of how the day-to-day has shifted, see Peek Into 2030: How SecOps Roles Will Change for the Better with AI Teammates.
What Does a SOC Analyst's Daily Work Look Like in 2030?
What Did the Old SOC Analyst Daily Rhythm Look Like?
He still remembers a specific shift in 2025 when he triaged 312 alerts in eight hours and went home not sure which ones he'd actually read. That was a normal day for the role.
Enterprises were processing more than 10,000 alerts daily across industries, and about half of them were never investigated, according to a systematic review of alert fatigue research published in ACM Computing Surveys.
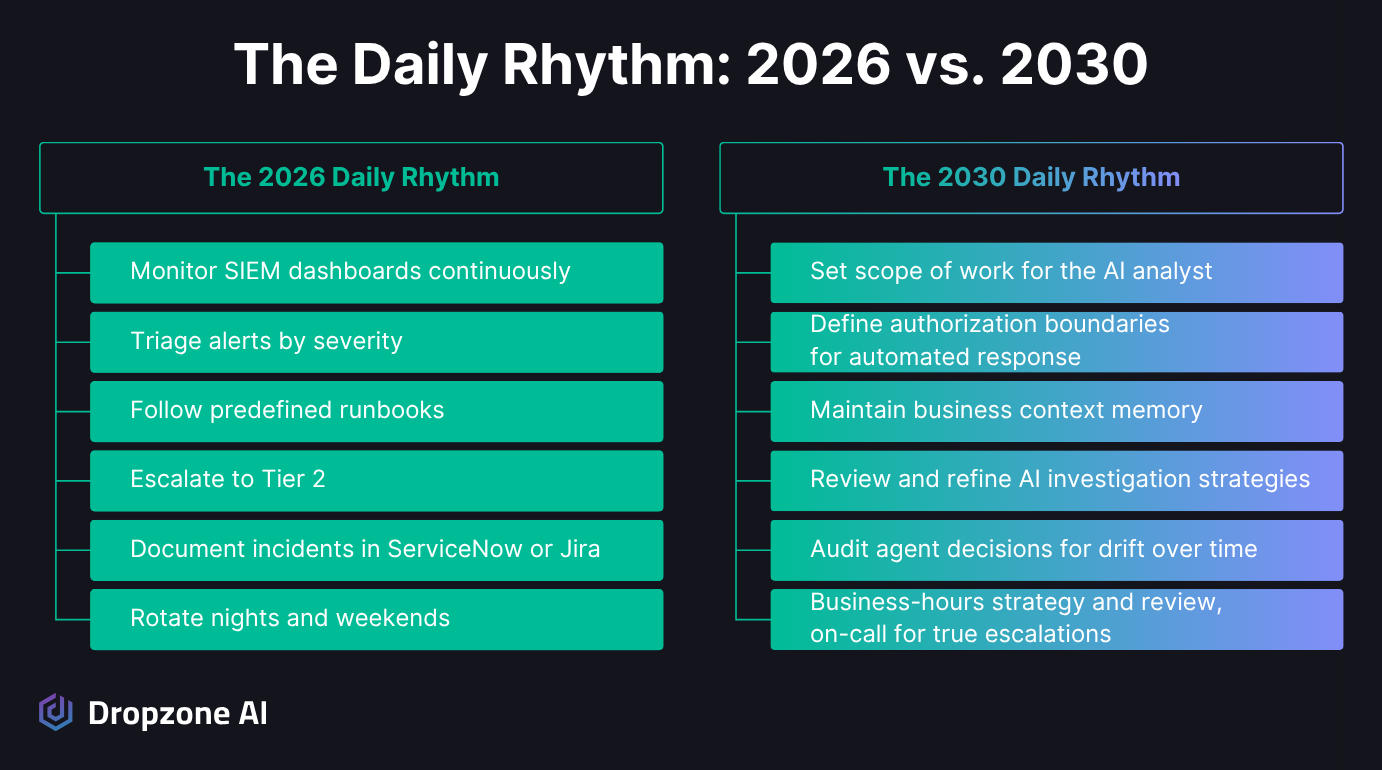
The 2026 JD on his screen reads like every Tier 1 SOC posting on Indeed and LinkedIn from that era:
- Monitor SIEM dashboards
- Triage alerts per the playbook
- Escalate to Tier 2
- Document in the ticketing system
- Rotate night and weekend shifts
The shift clause hasn't moved a centimeter from the version he answered.
When the agents landed in his SOC in 2027, half the team, including him, thought their jobs were ending. Reading that old JD now, the part that ages worst isn't the tech stack but the rhythm.
What Does the New SOC Analyst Daily Rhythm Look Like?
Every alert that hits his queue gets a full investigation in minutes from an AI agent. His team spends the saved hours shaping how those agents work rather than running through alerts themselves.
The human side of the job splits into three responsibilities:
- Setting the scope of work: what the agent investigates, how deep it goes, what it never touches
- Defining authorization: what actions the agent can take on its own vs. what it must escalate
- Maintaining the business context: the asset, identity, and process knowledge the agent reasons against
In the AI SOC Operator job description open on his screen, one of the lead responsibilities is writing the authorization policy that determines when the agent can disable a user account on its own and when it must escalate. This policy is not a rigid if-then-else logic playbook, but written in a way that humans or AI agents can read and follow. It is updated regularly based on the organization’s threat model.
That bullet about authorization didn't exist on any 2026 SOC posting. A 2025 Cloud Security Alliance benchmark study of AI agents in the SOC found AI-assisted investigations 45 to 61% faster and 22 to 29% more accurate, with the junior-to-senior performance gap narrowing under AI assistance.
A daily list in 2030 looks something like this:
- Refine what the agents investigate
- Approve or revise containment actions held for review
- Add new context as the environment changes
- Read agent investigations on high-severity alerts and feed corrections back
- Coach the agents on false positives the way you'd coach a new hire
That's what an operator's day actually looks like. If you're staring at a 2026 Tier 1 JD on your screen right now, that's the list to swap it for.
Who Do You Hire for a SOC Role in 2030?
Which SOC Analyst Skills Stopped Mattering?
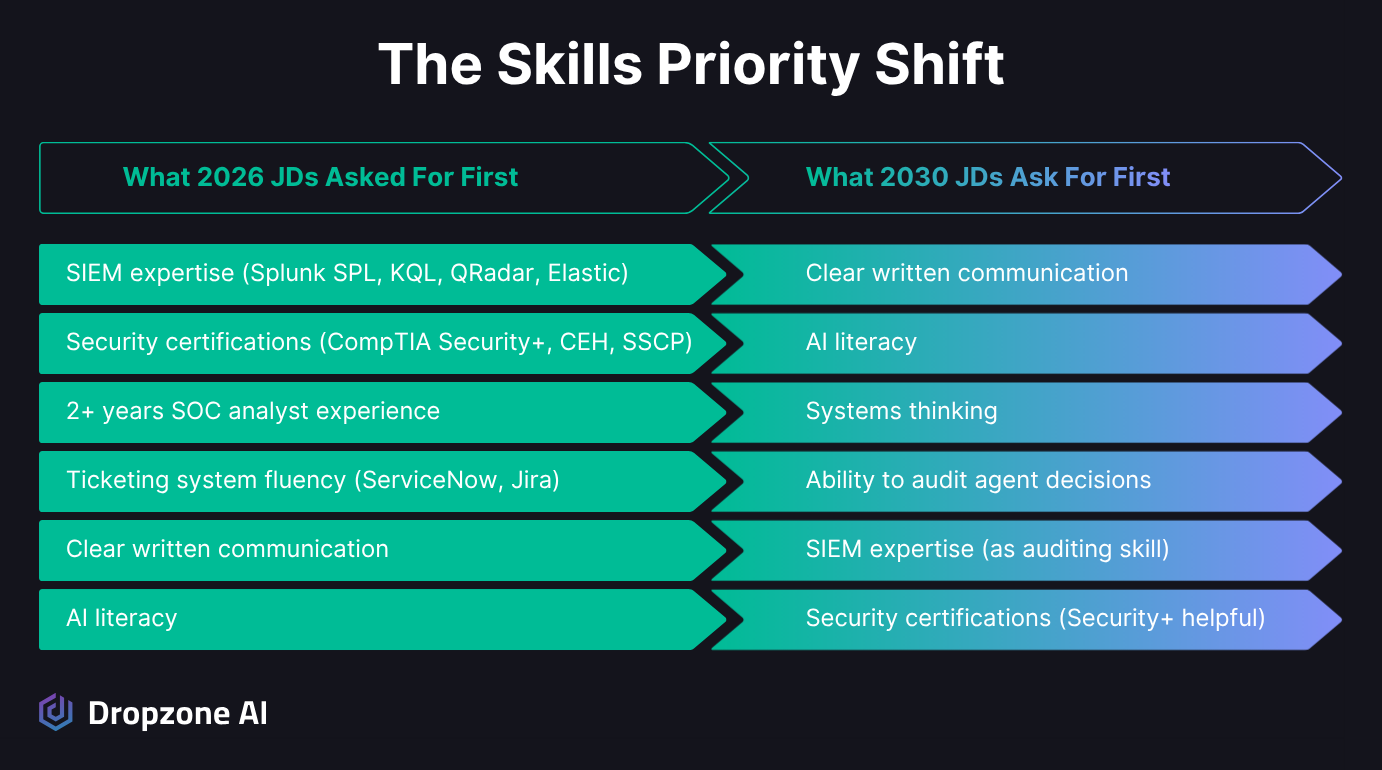
The 2026 JD on his screen opens with SIEM expertise: Splunk SPL, KQL, QRadar, Elastic, above any other technical skill. He remembers writing Splunk searches for nine hours a day and feeling like that was the job.
SIEM expertise was the single most commonly requested technical skill on SOC analyst postings in early 2026. His 2030 postings don't lead with it; they list it low down, framed as an auditing skill rather than a daily-use one.
In 2026, an analyst spent the day writing queries. In 2030, they spend it writing direction:
- Agent instructions (written in natural language, not as SOAR playbooks)
- Context updates
- Authorization policy
- Correction notes that go back into context memory
The SIEM still does what it always did; the analyst's role within it has changed.
The same shift hit certifications. He keeps Security+ on as "helpful" but pulled CEH and SSCP off years ago, along with the "2 years SOC experience" filter that used to screen out half his strongest candidates.
Which SOC Analyst Skills Took Their Place?
Clear written communication is the first qualification on every JD he writes now. In 2026, it was a bullet near the bottom. AI literacy follows written communication as the second lead qualification, framed in his JDs as hands-on rather than nice-to-have.
Communicating with other humans and AI agents is a more critical skill than ever, and good writing is a sign of good communication skills.
The interview test now asks three things:
- Can the candidate read an agent's investigation and tell where the reasoning skipped a step?
- Can they write a policy that constrains an agent without breaking it?
- Can they spot when the model is confidently wrong?
He hasn't figured out how to interview cleanly for that last one. What he’s looking for is critical thinking that is able to discern when AI is getting it wrong, and understanding how context engineering can break down. Three of his last six hires in this category were borderline calls he almost passed on. They've turned into some of his best operators, and he isn't sure whether his current screen is selecting for the right people or just getting lucky.
Candidates who do AI work well don't always come with the longest security resumes. The ISC2 2025 Cybersecurity Workforce Study ranked AI as the top skill need among cybersecurity teams, cited by 41% of respondents, ahead of cloud security at 36%.
Maya, his strongest hire in 2029, came from a junior SRE background. Her interview answer that locked it in: "I'd rather read the agent's reasoning chain than the alert." That's the systems thinking the new role rewards, the same way a platform engineer reasons about a service.
For the broader career-arc context behind that shift, see Dropzone's SOC Analyst Career Path & Salary Guide (2026 AI-Powered Edition).
How Did the SOC Team Get Shaped Differently?
Which SOC Roles Grew Up?
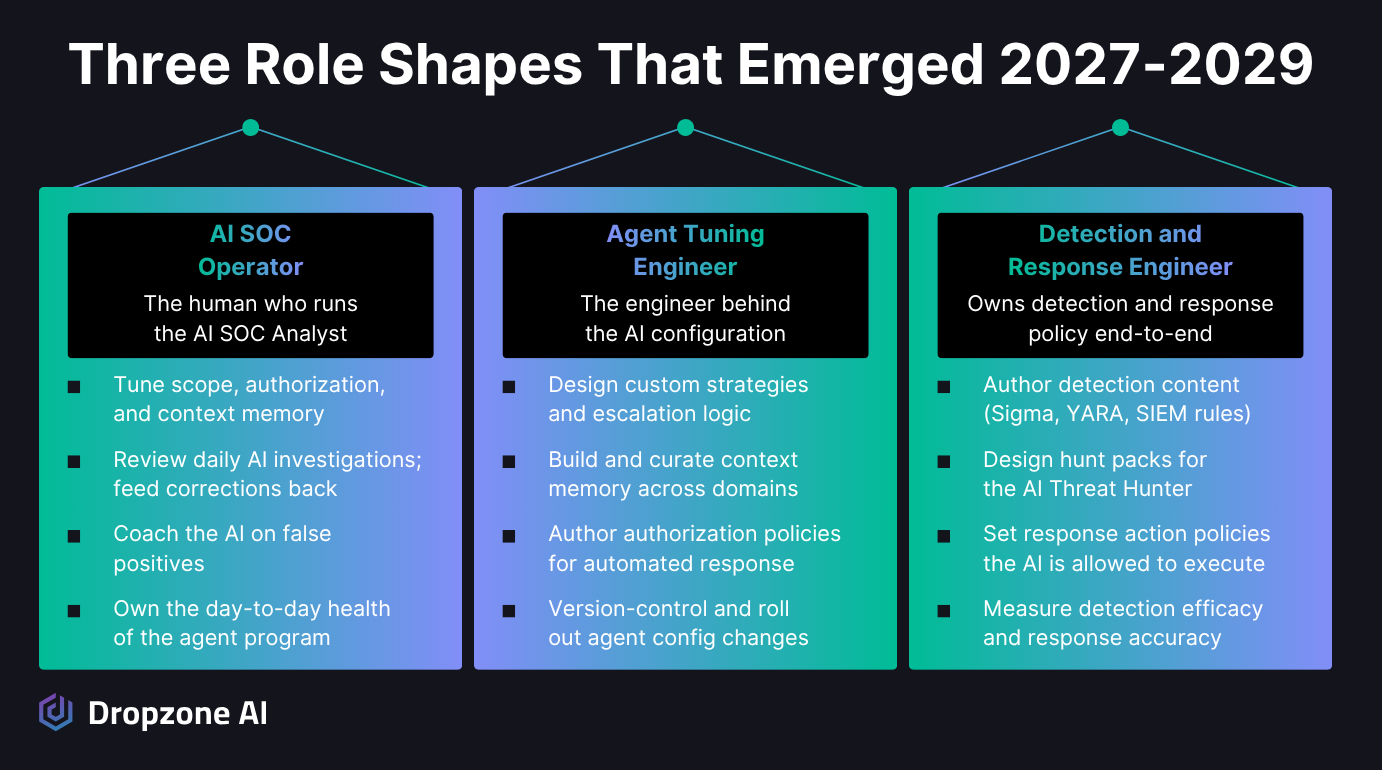
The SOC manager’s senior analyst now spends most of the week on actual senior work. In 2026, the same role meant constantly being pulled off strategic projects to firefight at 2 am, with proactive security activities like hunt design, detection engineering, tabletop exercises, and purple team exercises all pushed to "next sprint," which never came.
The 2 am pages stopped years ago.
Today, the senior on his team handles the following without distracting interruptions:
- Threat modeling for the environment
- Hunt direction for the agent layer
- Tabletops grounded in real findings (not generic scenarios)
- Architecture conversations with cloud and application engineering teams
- Mentoring the operators who run the agent layer day-to-day
Senior analysts who used to leave for jobs where they could actually do senior work are staying.
He also merged detection engineering and response into one role in 2029. The line between "what we hunt for" and "what the agents are allowed to act on" has stopped reading as two separate jobs.
He has more senior people on the team than at any point since he took the manager job, which aligns with the SANS 2025 SOC Survey finding that analyst tenure has stabilized, automation having landed, after years in which roughly 70% of analysts with under five years of experience left within three years.
Which SOC Roles Didn't Exist Before?
He's hiring for one role this quarter that didn't exist on the careers page in 2026: SOC Agent Engineer. Think of it as detection engineering, except that the artifacts are agent strategies and context memory rather than rules.
The day-to-day looks more like platform engineering than 2026 detection work:
- Versioned configurations
- A/B-tested investigation strategies
- Rollback procedures for context updates that degrade accuracy
- Incident response procedures for when the agent layer itself has a bad day
By early 2029, the agent configuration work had outgrown what any of his operators could handle as a side responsibility, and it needed a dedicated owner.
Most of these new role shapes weren't external hires anyway: his detection engineer took on managing response policy when he merged the two functions, and his senior IR engineer became the first agent tuning lead, starting in that role in February of last year. Teams don't add the role until they need it. The cue: nobody on the team can clearly say who owns the agent configuration end-to-end.
His total team size matches 2026, but the distribution of work across it is different. The hours that used to fill an entire Tier 1 floor are now spread across investigation review, senior strategy, agent tuning, and the new agent-layer role.
People on the team work shorter weeks, and the numbers he takes into board reviews hold up under questions. The biggest tell that the work has changed isn't on his career page. It's that he hasn't pulled an all-nighter in 18 months.
Conclusion
He closes the old JD tab and looks at the blank template. Back in 2026, he spent six months quietly job-hunting, in case he needed to leave the field. He didn't end up using the resume he updated. The work changed, the team didn't shrink, and the people who stuck around ended up doing more interesting work than they had before.
If you're rewriting a JD this quarter, three moves help:
- Promote clear writing and AI literacy above SIEM expertise in the qualifications section.
- Drop the years-of-experience filter that screens out the candidates who do this work best.
- Write the responsibilities around the system the candidate will operate, not the queue they'll sit at.
Want to see what enables the shift in SOC roles? See for yourself in the Dropzone self-guided demo, a live environment where you can explore real investigations on your own.