Threat Hunting. Powered by AI SOC Analysts
Our AI SOC analyst finds threats others miss. It cuts investigation time by 95%, freeing your team from endless alert analysis to focus on proactive threat hunting.
5x
faster mean time to respond
85%
reduction in manual alert investigation
300+
deployments worldwide

Gartner Cool Vendor for the Modern SOC
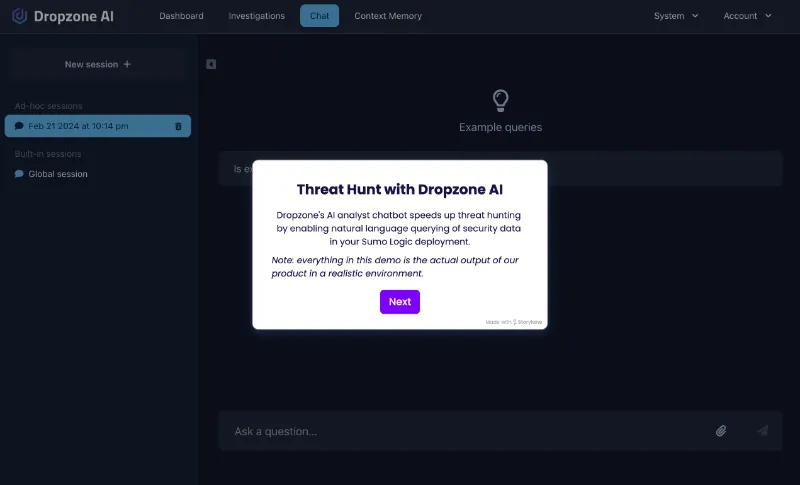
Query Dropzone's AI SOC analyst to accelerate threat hunting. It autonomously investigates security data, reasons across thousands of alerts, and identifies real threats faster than any human Tier-1 analyst.
Collect
Dropzone AI automatically identifies the optimal data sources across your security ecosystem for each investigation. It generates precise, native queries for your specific security tools—such as SPL queries for Splunk—eliminating the manual effort of navigating multiple interfaces to gather critical security evidence.
Comprehend
Our AI SOC Anlalyst's advanced LLM system methodically breaks down complex security inquiries into logical investigation steps. By reasoning through hundreds of records and intelligently gathering evidence, it identifies real threats that require your team's attention, separating signal from noise.
Conclude
We deliver clear, actionable threat assessments in seconds. Each investigation produces a structured report with evidence, attack indicators, and severity ratings—so your team can immediately focus on legitimate threats that require human expertise.
Integrations
Dropzone AI connects with your SIEM, EDR, and cloud security tools, enabling threat hunting across your entire security ecosystem without new infrastructure.



.svg)





.svg)


Proactive Threat Hunting Without the Wait
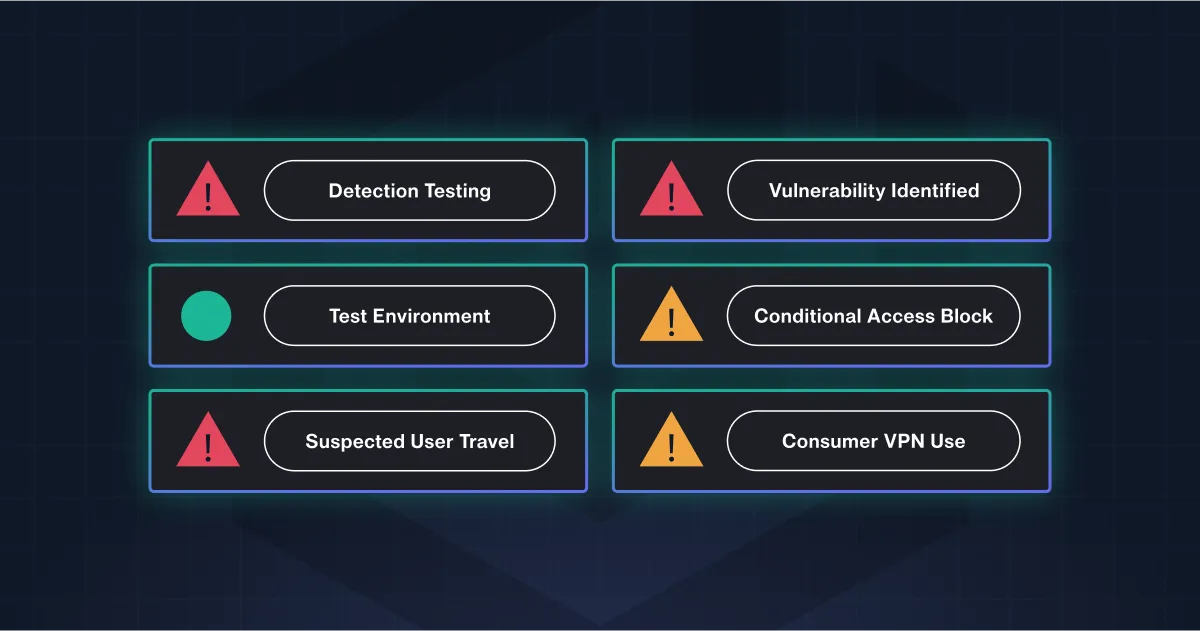
Dropzone automatically investigates every security alert in under 3 minutes, allowing SOC analysts to focus time on proactive threat hunting instead of alert triage.
Reduce MTTR
Eliminate investigation delays by immediately initiating alert analysis as soon as threats are detected. Automated data collection across security tools cuts investigation time from hours to minutes, dramatically reducing your Mean Time to Resolution.
Focus on real threats
Dropzone's advanced LLM system methodically breaks down complex security inquiries into logical investigation steps. By reasoning through hundreds of records and intelligently gathering evidence, it identifies real threats that require your team's attention, separating signal from noise.
Free your analysts for higher-value work
Dropzone summarizes key investigation findings into clear, natural language reports that your team can immediately understand and act on. This eliminates manual analysis time, freeing your security analysts to focus on what matters most—proactive threat hunting and staying ahead of attackers.
Want to test drive
Dropzone AI?
Note about privacy:
- All emails are deleted after analysis
- No emails will be used to train AI models
- We will collect the email address that is submitted and add it to our mailing list. You may unsubscribe at any time.
By using our service, you agree to the above
Forward a suspicious email to scan@try-dropzone.ai

Dropzone AI Investigates

Receive Tailored Report

- All emails are deleted after analysis
- No emails will be used to train AI models
- We will collect the email address that is submitted and add it to our mailing list. You may unsubscribe at any time.
By using our service, you agree to the above
Get a sample report




.webp)


.webp)


.webp)